Release 5.1.0
Copyright © 2019 DF/Net Research, Inc.
All rights reserved. No part of this publication may be re-transmitted in any form or by any means, electronic, mechanical, photocopying, recording, or otherwise, without the prior written permission of DF/Net Research, Inc.. Permission is granted for internal re-distribution of this publication by the license holder and their employees for internal use only, provided that the copyright notices and this permission notice appear in all copies.
The information in this document is furnished for informational use only and is subject to change without notice. DF/Net Research, Inc. assumes no responsibility or liability for any errors or inaccuracies in this document or for any omissions from it.
All products or services mentioned in this document are covered by the trademarks, service marks, or product names as designated by the companies who market those products.
Google Play and the Google Play logo are trademarks of Google LLC. Android is a trademark of Google LLC.
App Store is a trademark of Apple Inc.
Feb 01, 2019
Abstract
This guide describes the DFcollect app.
The instructions are intended to describe, in general terms, how data entry tasks are performed using DFcollect. The guidance provided here is not meant to replace more specific instructions which may be provided by the sponsor, principal investigator or coordinating site for a particular trial.
Table of Contents
- Preface
- 1. Introduction
- 2. Data Entry
- 3. Metadata
- 4. Working Offline
- A. Copyrights - Acknowledgments
- A.1. External Software Copyrights
- A.1.1. DCMTK software package
- A.1.2. Jansson License
- A.1.3. HylaFAX Facsimile Software
- A.1.4. Mimencode
- A.1.5. RSA Data Security, Inc., MD5 message-digest algorithm
- A.1.6. mpack/munpack
- A.1.7. TIFF
- A.1.8. PostgreSQL
- A.1.9. OpenSSL License
- A.1.10. Original SSLeay License
- A.1.11. gawk
- A.1.12. Ghostscript
- A.1.13. MariaDB and FreeTDS
- A.1.14. QtAV
- A.1.15. FFmpeg
- A.1.16. c3.js
- A.1.17. d3.js
Table of Contents
DFcollect is a tablet-based app for data collection in support of a DFdiscover study.
DF/Net Research, Inc.'s Technical Support Department can be contacted Monday to Friday between 9:00 am and 5:00 pm Eastern Time via any of the following methods:
55 Head Street, Suite 403
Dundas, Ontario L9H 3H8
Telephone: (905) 522-3282
Email: <support@datafax.com>
URL: www.dfnetresearch.com
DF/Net Research, Inc. provides an automated email mailing list for tips, help, and interaction with other DFdiscover users.
To subscribe to the mailing list, complete the simple form found at the DFdiscover User's Group mailing list webpage. It is also possible to unsubscribe from the mailing list by visiting the same webpage.
To submit a message to the mailing list
-
Subscribe to the list. Message submissions are only accepted from members of the list.
-
Create your email message.
-
Send the email message to
<DFUG@datafax.com>.
A number of conventions have been used throughout this document.
Any freestanding sections of code are generally shown like this:
# this is example code code = code + overhead;
If a line starts with # or %, this
character denotes the system prompt and is not typed by the user.
Text may also have several styles:
Emphasized words are shown as follows: emphasized words.
Filenames appear in the text like so:
dummy.c.Code, constants, and literals in the text appear like so:
main.Variable names appear in the text like so:
nBytes.Text on user interface labels or menus is shown as: Printer name, while buttons in user interfaces are shown as .
Menus and menu items are shown as: > .
Table of Contents
DFcollect is a tablet-based mobile application that allows users to perform online and offline data collection for a DFdiscover study.
DFcollect is distributed on Google Play™ for Android™ devices and the Apple® App Store® for iOS® devices.
DFcollect requires a device running Android™ 5.0 or greater, or iOS® 10 or greater. The user interface is optimized for tablets. The minimum screen resolution is 800 x 600 and the minimum memory requirement is 2GB. The device must have Wi-Fi and/or cellular communication capabilities.
The main purpose of DFcollect is to facilitate data collection using a mobile device at clinical sites participating in a DFdiscover study. For users that need to collect clean data, in online and offline settings, and do not need the extended feature set of DFexplore, DFcollect is the perfect tool.
DFcollect includes several data validation features including legal range checking, type validation, required values, field skipping, missing value coding, and edit checks, plus several metadata features, including adding, resolving, and editing queries, and adding reasons for data values. Management of study documents related to clinical subjects is also available.
DFcollect includes several key pages, menus, and dialogs to facilitate data entry. These pages are explained here, and the terminology used in this document and DFcollect is defined. More detailed explanations of key screens and functionality are given in the following sections.
DFcollect is an installed app. DFcollect is available on Google Play™ and Apple® App Store®. It must be downloaded and installed before use.
Once installed on your device, DFcollect has the following appearance:
![]() .
.
DFcollect is distributed on Google Play™ for Android™ devices and the Apple® App Store® for iOS® devices. Once DFcollect is installed on the device, select the app icon to open DFcollect. The login page is the initial landing page in DFcollect.

To access a study, a successful login is required. Successful login requires valid credentials. Valid credentials include a value for each of DFdiscover Server, Username and Password. Your study sponsor or monitor has provided you with your own unique credentials. After login, all activities are logged with your username. Do not share your credentials with any other user. Each user must use their own credentials.
If you already have login credentials for other DFdiscover tools, the login credentials for DFcollect are identical.
Once you have entered a value for DFdiscover Server, the login screen may refresh with a standard message from the DFdiscover administrator. This is useful confirmation that you are connecting to the correct server.
Enter your Username and Password exactly as provided. Click to continue.
Problems with the login, whether due to a bad password, mistyped server, or anything else, may appear in red text below the login button.
When you login for the first time, or if your password expires, you may be prompted to provide a new password. To continue provide a new password meeting the stated requirements.
To exit from DFcollect, choose from the Application Menu. After successful logout, the login window is shown.
When using DFcollect, logging out via in the Application Menu is the recommended and most secure way to exit DFcollect. Although closing the app ensures your data is safe, it is best practice to logout properly.
In addition to the login page, there are several intermediate pages. These pages allow the user to select a study, site, visit, and finally a CRF for data entry.
The main application page is the primary interface for most data entry tasks. This page has the following features:
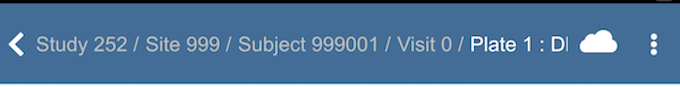
Header Panel. The header panel is available on all pages of DFcollect except the login page. It contains options and navigation that are relevant for the current page, including:
Breadcrumb. The breadcrumb is a navigation aid displaying information about the current context as well as simplifying access to other pages in the study via clickable links.
Application Menu. The application menu, accessed by clicking
 or
or  , contains several generic functions that are
not study specific, including , , and .
See Application Menu for more information.
, contains several generic functions that are
not study specific, including , , and .
See Application Menu for more information.
Main Panel. The main panel contains the primary information and interaction for the current page. Pages that may appear here are the Studies Page, Sites Page, Subjects Page, Subject Binder, and Data Entry Form.
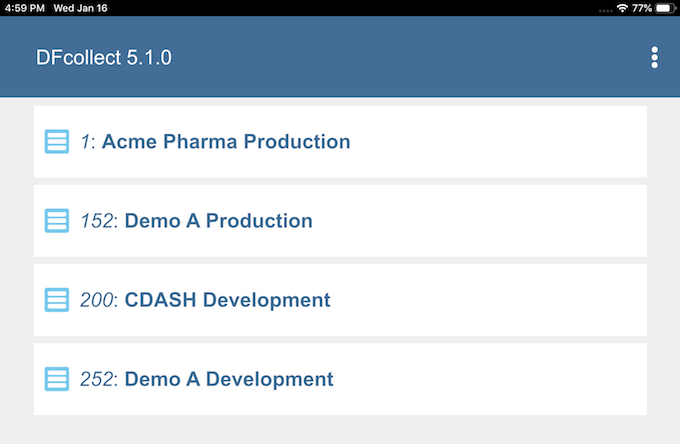
The Studies Page is the first page you navigate to after successful login. It lists the studies you have permissions for. Click one of the available studies to choose that study. This takes you to the Sites Page for that study.
If you have permissions for exactly one study, this page is bypassed, going to the Sites Page.
The study number, name, and status are displayed on each line. If the study is not available, the icon will be displayed as  . Click the study name to show the reason that the study is not available.
. Click the study name to show the reason that the study is not available.

The Sites Page contains a list of the sites you have permission for. The site number and label are shown, one per row. Click one of the sites to make it the active site. This takes you to the Subjects Page for that site.
The Sites page also includes search functionality. Click  to display the search field, enter the search term, and click
to display the search field, enter the search term, and click  again to see the results. Use
again to see the results. Use  and
and  to navigate between multiple search results. Select
to navigate between multiple search results. Select  to return to the top of the page.
to return to the top of the page.
If you have permissions for exactly one site, this page is bypassed, going to the Subjects Page.
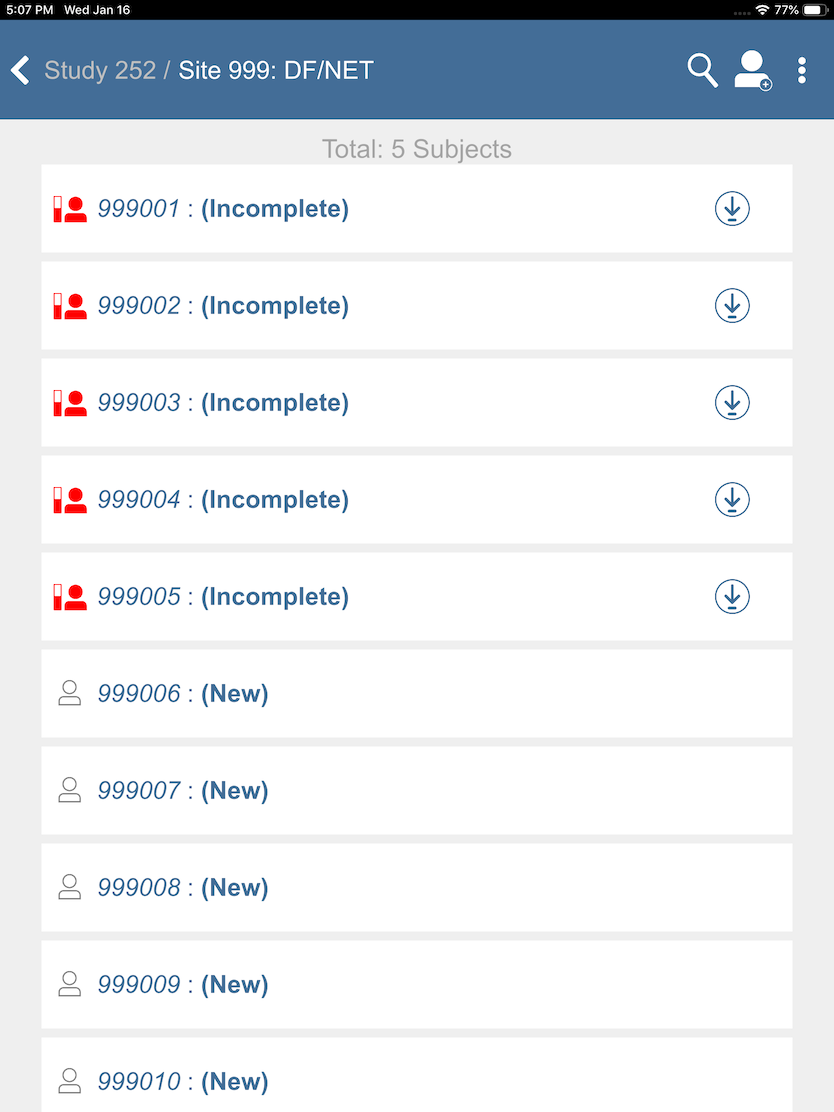
The Subjects Page contains a list of permitted subjects. Click a subject to go to the subject binder. The icon to the left of the subject ID shows the current status of the subject binder. The status may change over the duration of the study as more visits become required and further data review takes place.
-
 The subject binder is final, all data required at this time
has been
submitted, and there are no outstanding responses or missing,
required values.
The subject binder is final, all data required at this time
has been
submitted, and there are no outstanding responses or missing,
required values.
-
 The subject binder is incomplete.
There may be missing, required values, illegal values
or unresolved questions about the data.
The subject binder is incomplete.
There may be missing, required values, illegal values
or unresolved questions about the data.
-
 The subject binder is pending.
There may be at least one document attached to the subject ID or pending data submitted for this subject.
The subject binder is pending.
There may be at least one document attached to the subject ID or pending data submitted for this subject.
-
 There is no data for this subject,
or the subject has not yet been saved.
There is no data for this subject,
or the subject has not yet been saved.
The Subjects Page also provides the following functionality:
Search Bar. The search bar allows you to quickly navigate to a subject with a given subject ID. Click
 to display the search field, enter the subject ID to search for, and click
to display the search field, enter the subject ID to search for, and click  again to see the results. Use
again to see the results. Use  and
and  to navigate between multiple search results. Select
to navigate between multiple search results. Select  to return to the top of the page.
to return to the top of the page.Add Subject. Click
 to open the Add Subject Dialog.
to open the Add Subject Dialog.
The Subject Binder contains all of the visit and CRF information related to the current subject. Further details regarding the Subject Binder can be found in Chapter 2, Data Entry and Chapter 3, Metadata. An overview is provided here.
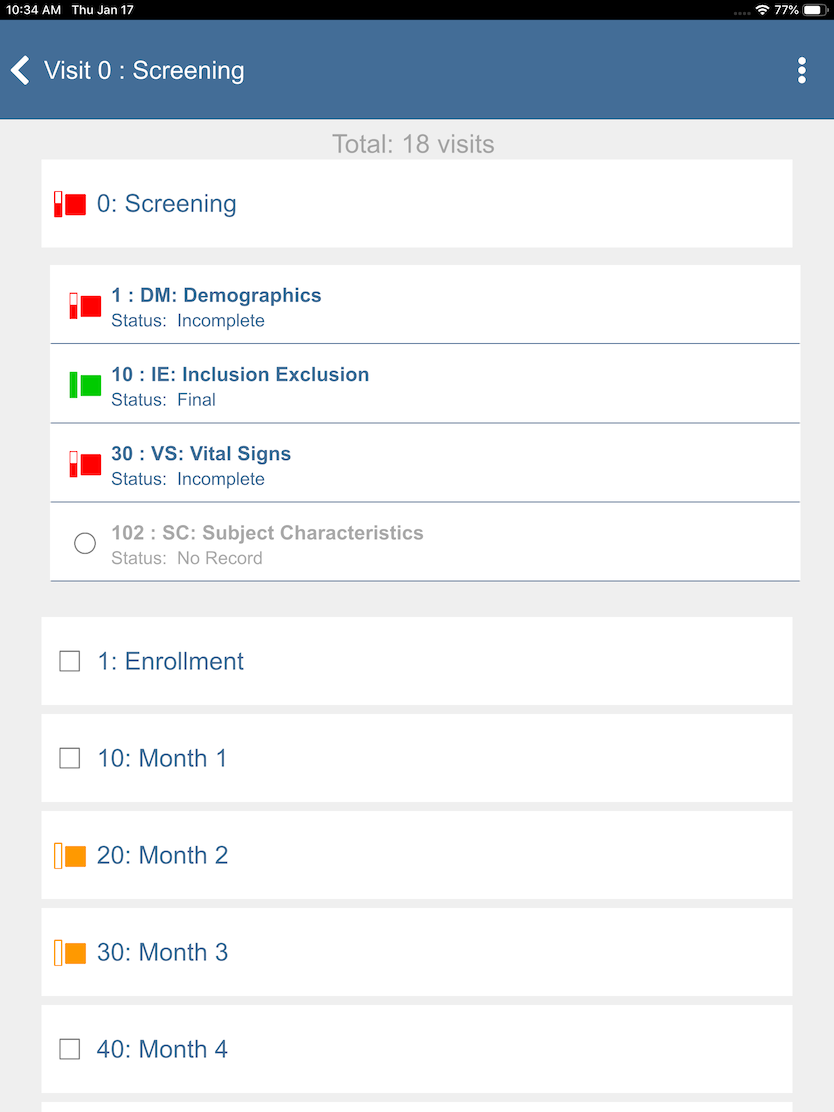
The subject binder displays the list of visits and CRFs for the selected subject. The breadcrumb at the top of the screen displays the study number, site number, and subject ID. The main body of the page displays, for the subject ID, all of the visits that you have permission to view.
Click any visit to expand it and show all the CRFs in that visit that you have permission to view. CRFs are indented slightly from the visits and shown in a smaller font to help visually differentiate them. CRF and visit labels follow the format [Number]: [Label].
Each visit and CRF has an icon that displays its current status. The meanings of the icons are:
 - This CRF or visit is final, and it is a required CRF or visit.
- This CRF or visit is final, and it is a required CRF or visit. - This CRF or visit is incomplete, and it is a required CRF or visit.
- This CRF or visit is incomplete, and it is a required CRF or visit. - This CRF or visit is pending, and it is a required CRF or visit.
- This CRF or visit is pending, and it is a required CRF or visit. - This CRF or visit has not been saved, and it is a required CRF or visit.
- This CRF or visit has not been saved, and it is a required CRF or visit. - This CRF or visit is final, and it is an optional CRF or visit.
- This CRF or visit is final, and it is an optional CRF or visit. - This CRF or visit is incomplete, and it is an optional CRF or visit.
- This CRF or visit is incomplete, and it is an optional CRF or visit. - This CRF or visit is pending, and it is an optional CRF or visit.
- This CRF or visit is pending, and it is an optional CRF or visit. - This CRF or visit has not been saved, and it is an optional CRF or visit.
- This CRF or visit has not been saved, and it is an optional CRF or visit. - This CRF or visit is final, and it is an unexpected CRF or visit.
- This CRF or visit is final, and it is an unexpected CRF or visit. - This CRF or visit is incomplete, and it is an unexpected CRF or visit.
- This CRF or visit is incomplete, and it is an unexpected CRF or visit. - This CRF or visit is pending, and it is an unexpected CRF or visit.
- This CRF or visit is pending, and it is an unexpected CRF or visit.
Click a CRF in the current visit to open the CRF, or click a different visit to display the available CRFs for that visit.
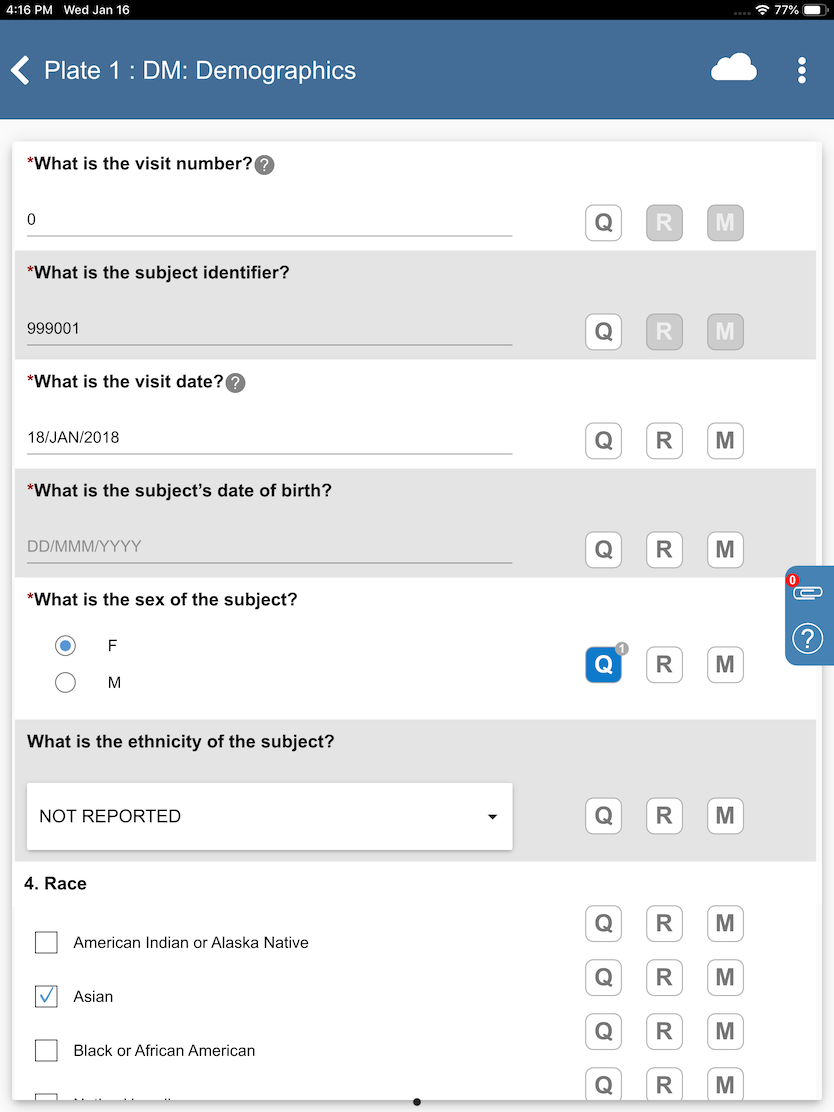
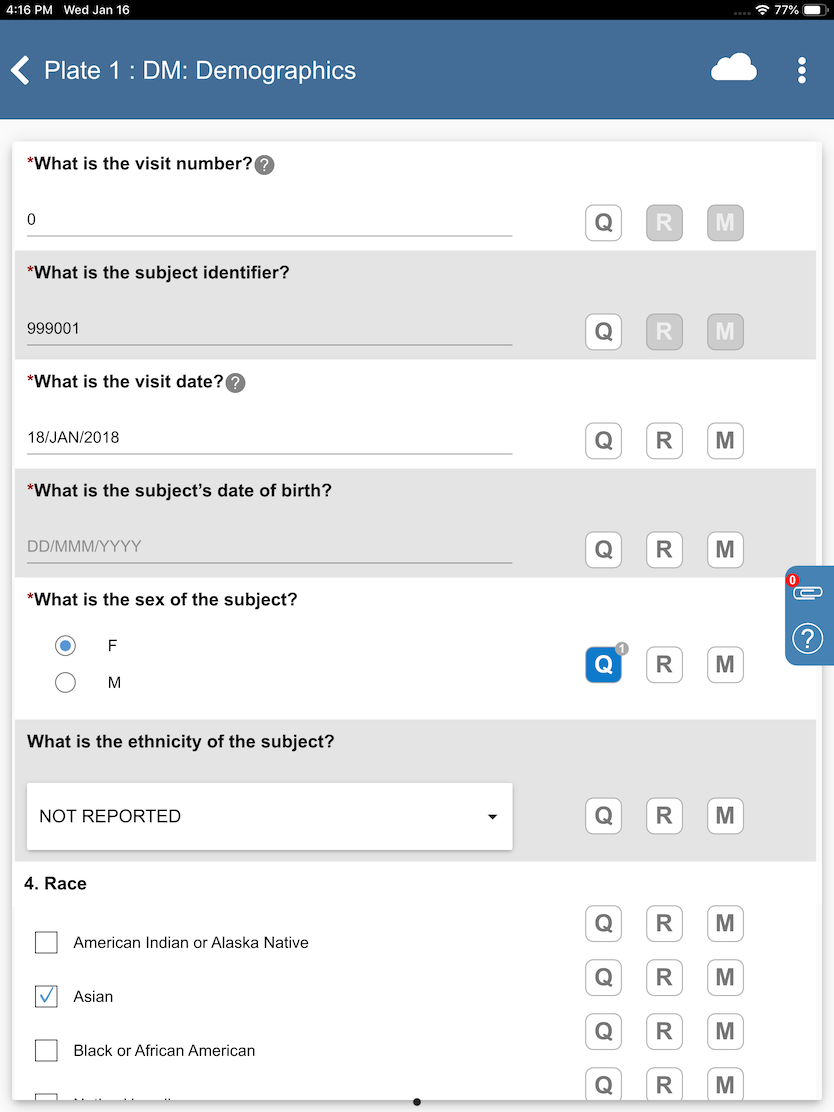
The main part of the page contains the data entry form. This form allows you to view, add and modify data, queries, reasons, and missing value codes, view and add documents to the CRF, and view available CRF help.
At the top of the form is a header area for CRF and study actions. The header remains visible as you scroll through the CRF contents. It contains:
CRF Label. The CRF label is composed of the CRF number and label. These follow the format [Number]: [Label]. The CRF label also functions as a breadcrumb. Swipe right to see the study, site, subject, and visit for the CRF, and click on any part to navigate back to that page.
Save Button. The appearance of the Save button changes depending on the connection status of the app (online/offline) and whether changes have been made to the CRF:
 - This CRF has not changed, and the app is online.
- This CRF has not changed, and the app is online. - This CRF has changed and is not yet saved, and the app is online. Click to save changes to the database.
- This CRF has changed and is not yet saved, and the app is online. Click to save changes to the database. - This CRF has changed and is not yet saved, and the app is offline. Click to save changes locally. See Working Offline for further details.
- This CRF has changed and is not yet saved, and the app is offline. Click to save changes locally. See Working Offline for further details. - The CRF changes have been saved successfully to the study database.
- The CRF changes have been saved successfully to the study database. - The CRF changes have been saved successfully to local storage, while offline. The changes must still be uploaded to the study database once back online.
- The CRF changes have been saved successfully to local storage, while offline. The changes must still be uploaded to the study database once back online. - This CRF is read only; it may be locked by another user or editing may not be permitted.
- This CRF is read only; it may be locked by another user or editing may not be permitted. - This CRF is read only based on user permissions.
- This CRF is read only based on user permissions.
Click
 to save the changes you have made to the current CRF and submit them to the server.
to save the changes you have made to the current CRF and submit them to the server.
Application Menu Button. Click
 to open the Application Menu, which contains study level options.
to open the Application Menu, which contains study level options.
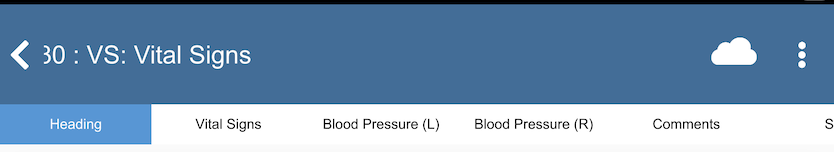
The remainder of the form contains the data entry area of the CRF. For CRFs using screens, they appear as tabs across the top of the data entry form.
Click the corresponding tab to go to that screen, or swipe left to go to the next screen and swipe right to go to the previous screen.
Each screen is composed of rows of fields. Rows are shaded with alternating color backgrounds. Each field can contain:
Field Label. The field label shows the field prompt, if it is available. Otherwise the field description is used for the label.
Field Input. Each field has an input area. The data type and format of the field determines exactly what appears in this area. For more information on input types, see Data Types.
Date Picker. Date fields have a date picker (
 ). Click to reveal a calendar. Picking a date in the calendar is equivalent to typing it in the Field Input.
). Click to reveal a calendar. Picking a date in the calendar is equivalent to typing it in the Field Input.Units. If units are defined for the field, they are shown in or near the input area. Where they are displayed depends on the type of input.
Field Help. If there is help information for the field,
 is visible. Click to display a help tooltip, which can be dismissed by clicking any other area of the page.
is visible. Click to display a help tooltip, which can be dismissed by clicking any other area of the page.Required Indicator. If the field is required or essential,
 appears on the line. Fields with this indicator display a warning message if left blank.
appears on the line. Fields with this indicator display a warning message if left blank.Metadata Indicators. , , and are displayed on each line. They allow the user to add, modify and view queries, reasons and missing value codes for that field. For more information on queries, reasons, and missing value codes, see Chapter 3, Metadata.
Focus Indicator. A colored vertical bar indicates that the field is in focus, and the color indicates the status of the field. To learn more, see Focus Indicators.
Warning Message. Warning messages appear when issues like illegal field values are present in the field. Correct the issue to remove the message.
On each data entry screen, the CRF Menu is positioned on the right side of the display, vertically centered. It provides options to view and upload documents and to view CRF help. See Section 1.4.2.2, “CRF Menu” for further details.
The application menu provides functionality applicable for the entire study or user session. Click  or
or  to access the application menu. The following options are available:
to access the application menu. The following options are available:
Preferences. Select to view and modify user and system settings. See Preferences for further details. This preference is only available after logging in.
About DFcollect. Select to view the version and build information about DFcollect.
Change Password. Select to change your password. See Change Password for further details. This preference is only available after logging in and while online.
Storage & Syncing. Select to view and manage records stored locally (for offline use) and to upload data saved while offline. See Working Offline for further details.
Study Help. Select to open a dialog with the help information defined for the study.
Logout. Select to exit the current study and return to the login page. Remember to always logout after completing your work.
The CRF Menu is visible only on the data entry form. It provides actions for the selected CRF. The following actions are available:
Manage Documents. Select
 to open the Manage Documents dialog. This allows you to add or view documents for the current CRF. The number in red is the number of documents attached to this CRF. See Managing Documents for further details.
to open the Manage Documents dialog. This allows you to add or view documents for the current CRF. The number in red is the number of documents attached to this CRF. See Managing Documents for further details.Page Help. Select
 to open the help information for this CRF.
to open the help information for this CRF.
Alert dialogs provide warnings of different events or states in DFcollect. Confirmation dialogs warn you of the (potentially unintended) consequences of an action you are about to perform and give you a option to cancel the action. Information in alert and confirmation dialogs is important, and you should read them carefully before closing them. Example dialogs include:
Error Dialogs. Error dialogs warn you of errors in DFcollect. These could be caused by a problem connecting to the DFdiscover server, or errors in DFcollect's functionality. The text in the dialog provides details as to what happened. Depending on the error, DFcollect may return to another page, logout, or stay on the current page.
Unsaved Changes Dialog. Navigating away from a CRF that has unsaved changes triggers an unsaved changes dialog. This dialog gives you a chance to stop the action and save those changes before continuing.
Session Timeout Dialog. If you have been away from DFcollect for too long, DFcollect logs you out. When this happens, a session timeout dialog is displayed. To continue you must login again.
On occasion, a change in the study setup can cause a value to be saved to the study database that can no longer be displayed in the field. In these cases, DFcollect modifies the values as best as possible to make them fit in the field. You are notified of these modifications with this dialog when you open the CRF.
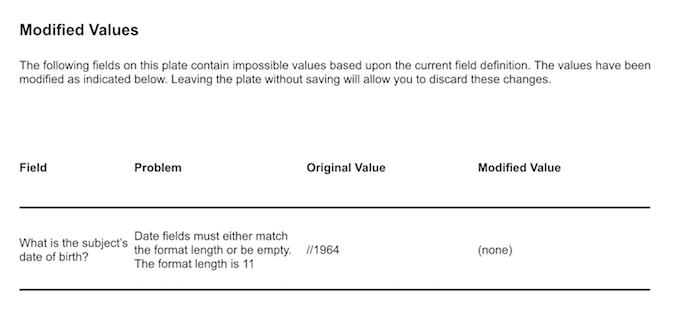
The dialog shows you a list of all fields modified in this way. For each field, the dialog shows you the field label, a message explaining why the value was modified, the value in the database, and what the value is after the modification.
Leaving the CRF without saving causes the modifications to be discarded and the database values to be preserved.
The Add Subject dialog is displayed after you click  on the Subjects Page.
Use it to start data entry for a subject ID that does not appear in the list.
The subject ID must be within the defined legal range for the site.
on the Subjects Page.
Use it to start data entry for a subject ID that does not appear in the list.
The subject ID must be within the defined legal range for the site.
To create a new subject, enter the desired subject ID in Enter Subject ID. Enter the same ID in Confirm Subject ID. When you have entered an ID in both input areas and no errors are displayed, click to create the subject. The subject binder page for the new subject is displayed. Click to close the dialog without creating a new subject.
The Query Dialogs allow you to create ( ),
edit (
),
edit ( ),
reply to (
),
reply to ( ) and
delete (
) and
delete ( ) queries for a field. Separate dialogs are used for each function.
Your permissions may not grant you access to all of the functions.
For a study in which multiple
queries are permitted per field, there is an additional Multiple Queries dialog to view and initiate actions once a query has been created for the field.
Click to open the query dialogs for the field.
For more details on query dialogs and their use, see Queries.
) queries for a field. Separate dialogs are used for each function.
Your permissions may not grant you access to all of the functions.
For a study in which multiple
queries are permitted per field, there is an additional Multiple Queries dialog to view and initiate actions once a query has been created for the field.
Click to open the query dialogs for the field.
For more details on query dialogs and their use, see Queries.
The Reason Dialogs allow you to create, edit, and delete reasons for a field. Your permissions may not grant you access to all of the functions. Separate dialogs are used for each function. Click on the field's row to open the reason dialog. For more details on the reason dialog and its use, see Add a Data Reason.
A Missing Value Code is a standard way to record that there is no response for a field and code the reason why. The Missing Value Code dialog allows you to set (or unset) a missing value code for the field. Click to open the Missing Value Code dialog. For more details on missing value codes and their use, see Mark a Data Value as Missing.
A glossary of frequently used terms is presented below.
Document |
A document is a file that is, or will be, attached to a CRF. Documents can be images, PDFs, videos or other file types. |
Field |
A field is a single data value and optional related metadata, including queries, the reason for the data value, possibly a missing value code, and other descriptive information about the field, such as its label and help. In DFcollect, fields are presented as rows in screens. |
Final (Status) |
Final is a record status. A record can have status Final if there are no missing required fields, no illegal values and no outstanding queries. DFcollect marks Final records with a green shaded rectangle (see also Incomplete and Pending). |
Incomplete (Status) |
Incomplete is a record status. A record can be saved with status Incomplete if it has one or more fields which are incomplete (required and missing) or illegal, or outstanding queries. DFcollect marks Incomplete records with a red partially shaded rectangle (see also Final and Pending). |
Missing Value Code |
A missing value code is used to identify a field that is known and accepted as empty. Used proactively, a missing value code can reduce the need for a query and explanation for a blank field. A missing value code allows even a required field to be blank and for the CRF to still be saved as Final. |
New (Status) |
New is a record status. A new record is a placeholder for data that has been entered but not saved yet. It can be a useful reminder for records which are expected but are not yet entered/saved. DFcollect marks new records by an empty grey square, circle, or subject icon without a rectangle. |
Pending (Status) |
DFcollect saves CRFs as Pending after a document has been added to a new CRF but no data entry has been done. DFcollect marks pending records with an orange empty rectangle. |
Plate, or CRF |
Plate and CRF are terms used interchangeably to refer to a logical grouping of data fields, presented with a layout determined by the study sponsor, to fit on a single sheet of paper or on one or more screens. Each CRF may stand alone, or CRFs may be grouped into multi-CRF forms. A collection of CRFs (or forms) constitute a visit, and a collection of visits constitute the subject binder, which holds all study data for an individual subject. |
Query |
A query is a question or comment about an individual data value. The study coordinating site may add a query to any data field to request a correction or clarification. A query is metadata about the data value, or lack thereof, in the field. DFcollect identifies query status by applying color to the field. A field with an outstanding query is blue. When a reply is provided to a query, or a reason is added to explain the field, the color is updated to orange, and when the field has been corrected, or the reply or reason have been approved, the color changes to green, provided there are no other outstanding queries on the field. |
Reason |
A reason is metadata used to explain the value in a data field. It is particularly useful as a way of explaining unusual values and thereby avoiding a data query from the study coordinating site. DFcollect colors fields with a new reason orange and gives them a Pending status. If the coordinating site accepts the reason, the field color changes to green and the reason status changes to Accepted. If they do not accept the reason, the field color changes to blue and the reason status changes to Rejected. A reason can be modified, which starts the review process over again. |
Save |
None of the changes made to a CRF are saved to the study
database (if online) or to local storage (if offline)
until you save the changes using |
Screen |
A screen is an optional grouping of fields on a CRF. On smaller displays, screens can be useful for grouping fields to ensure that they are seen together. DFcollect indicates screens using tabs at the top of the data entry form. Select the appropriate tab or swipe to move between screens. |
Subject |
A subject is an individual participating in a clinical study and for whom data is collected. Subjects are identified by subject ID (a unique numeric identifier), according to conventions established by the study coordinating site. |
Subject Binder |
A subject binder contains all of the required and optional data collection forms used to collect study data for an individual subject. Within DFcollect, subject binders are displayed in a list by subject ID, with an associated icon that indicates whether the binder is empty or contains recorded data, and whether that data is currently Final, Incomplete or Pending. |
Visit |
A visit is a study timepoint at which one or more CRFs for a subject are completed, or a repeating log form such as an adverse event or concomitant medications. The duration of a subject's participation in a study is often marked by a baseline visit, several repeating visits, and a termination visit. |
Click  or
or  and select to view and modify user and system settings. Preference changes are limited to the current device and user.
and select to view and modify user and system settings. Preference changes are limited to the current device and user.
Exit After ... minutes of activity. This setting defines the amount of time DFcollect will remain inactive before the user is automatically logged out. Note that the actual logout timer interval may be longer than indicated on some devices (e.g. slower CPUs, older tablets). In most environments, a value between 10 and 20 minutes is optimal.
Read Only. Enable this setting to make all data and metadata read only. No changes to CRFs, queries, reasons, missing values, or documents can be made in DFcollect with this setting turned on. This is a useful setting for a reviewer who does have modify permissions and wants to ensure that they do not make changes inadvertently.
Download Documents. Enable this preference to include documents when downloading subject data for offline use. You may wish to disable this preference if you have limited storage space on your device. For further details, see Working Offline.
API Server. The API server name may be updated from the default, if required for your study as advised by the study coordinating site. This preference is only settable before logging in.
Server Connection. Enable this preference to login without connecting to the server (i.e. remain offline) even if you are connected to the internet. This is a proactive choice that is recommended if you will be offline or in a setting where connectivity is not stable. This preference is only settable before logging in.
To change your password, click  and select . The Change Password dialog opens, indicating the minimum password requirements. Enter a new password in New Password, then enter the same password again in Confirm Password.
and select . The Change Password dialog opens, indicating the minimum password requirements. Enter a new password in New Password, then enter the same password again in Confirm Password.
If the password does not meet the requirements or the confirmed password does not match, an error message is displayed in red. Once any errors are resolved, select to save the new password. If the change does not succeed, an error message describes the problem. To close the dialog without changing your password, select .
When you open a CRF while online, DFcollect attempts to establish a lock on the CRF. If it succeeds, you gain the lock on the CRF and other DFdiscover users and apps will not be able to edit the CRF until it is unlocked. If someone else already has the lock, your attempt fails and you are shown the locked CRF in read-only mode.
A locked CRF is indicated by ![]() in the header. Saving is disabled. Data cannot be entered or modified, and no queries, reasons, or missing codes can be added to any fields. Existing queries, reasons, and missing codes can be viewed, as well as any attached documents.
in the header. Saving is disabled. Data cannot be entered or modified, and no queries, reasons, or missing codes can be added to any fields. Existing queries, reasons, and missing codes can be viewed, as well as any attached documents.
Leaving a CRF, by navigating to another CRF, visit, subject binder or logging out of DFcollect, unlocks the CRF.
To maintain security, the DFcollect login session is automatically closed if there is no activity for the amount of time defined in DFcollect Preferences (see Preferences for details). The default session timeout is 10 minutes. Keep the session active to avoid being logged out.
![[Note]](../../imagedata/note.png) | Note |
|---|---|
On some devices, the session timer may not be 100% accurate. The interval may be longer than indicated on slower CPUs or older devices. |
In the event of session timeout, the following actions take place:
an information dialog is presented to notify that the session has timed out
unsaved changes for the current CRF, if any, are discarded
the lock for the current CRF, if any, is released
you are logged out and taken back to the login screen
Never rely on the session timeout to terminate a session. Always save changes to the current CRF and logout.
This section lists all icons used in DFcollect along with their meanings.
 - Application menu icon, on the login page.
- Application menu icon, on the login page.
 - Application menu icon, after logging in.
- Application menu icon, after logging in.
 - Back icon. Click to return to the previous page.
- Back icon. Click to return to the previous page.
 - Study not available icon, on the Studies page. The current study is not available.
- Study not available icon, on the Studies page. The current study is not available.
 - Add subject icon on the Subjects page. Click to add a new subject not listed on the page.
- Add subject icon on the Subjects page. Click to add a new subject not listed on the page.
 - Search icon, on the Sites and Subjects pages. Click to display the search field and enter the site or subject ID to search for. Click again to display the first search result.
- Search icon, on the Sites and Subjects pages. Click to display the search field and enter the site or subject ID to search for. Click again to display the first search result.
 - Search down. Click to move to the next search result.
- Search down. Click to move to the next search result.
 - Search up. Click to move to the previous search result.
- Search up. Click to move to the previous search result.
 - Return to top. Click to return to the top of the page.
- Return to top. Click to return to the top of the page.
 - Final subject binder. All data required at this time have been submitted, and there are no outstanding queries or missing required values.
- Final subject binder. All data required at this time have been submitted, and there are no outstanding queries or missing required values.
 - Incomplete subject binder. There may be missing required values, illegal values, or unresolved queries for this subject.
- Incomplete subject binder. There may be missing required values, illegal values, or unresolved queries for this subject.
 - Pending subject binder. There may be at least one document attached to the subject ID or pending data submitted for this subject.
- Pending subject binder. There may be at least one document attached to the subject ID or pending data submitted for this subject.
 - Blank subject binder. There is no data for this subject, or subject data has not yet been saved.
- Blank subject binder. There is no data for this subject, or subject data has not yet been saved.
 - This CRF or visit is final, and it is a required CRF or visit.
- This CRF or visit is final, and it is a required CRF or visit.
 - This CRF or visit is incomplete, and it is a required CRF or visit.
- This CRF or visit is incomplete, and it is a required CRF or visit.
 - This CRF or visit is pending, and it is a required CRF or visit.
- This CRF or visit is pending, and it is a required CRF or visit.
 - This CRF or visit has not been saved, and it is a required CRF or visit.
- This CRF or visit has not been saved, and it is a required CRF or visit.
 - This CRF or visit is final, and it is an optional CRF or visit.
- This CRF or visit is final, and it is an optional CRF or visit.
 - This CRF or visit is incomplete, and it is an optional CRF or visit.
- This CRF or visit is incomplete, and it is an optional CRF or visit.
 - This CRF or visit is pending, and it is an optional CRF or visit.
- This CRF or visit is pending, and it is an optional CRF or visit.
 - This CRF or visit has not been saved, and it is an optional CRF or visit.
- This CRF or visit has not been saved, and it is an optional CRF or visit.
 - This CRF or visit is final, and it is an unexpected CRF or visit.
- This CRF or visit is final, and it is an unexpected CRF or visit.
 - This CRF or visit is incomplete, and it is an unexpected CRF or visit.
- This CRF or visit is incomplete, and it is an unexpected CRF or visit.
 - This CRF or visit is pending, and it is an unexpected CRF or visit.
- This CRF or visit is pending, and it is an unexpected CRF or visit.
 - The CRF save button when the CRF has not changed and the app is online.
- The CRF save button when the CRF has not changed and the app is online.
 - The CRF save button when the CRF has not changed and the app is offline.
- The CRF save button when the CRF has not changed and the app is offline.
 - The CRF save button when the CRF has changed and is not yet saved, and the app is online. Click to save changes to the database.
- The CRF save button when the CRF has changed and is not yet saved, and the app is online. Click to save changes to the database.
 - The CRF save button when the CRF has changed and is not yet saved, and the app is offline. Click to save changes to local storage.
- The CRF save button when the CRF has changed and is not yet saved, and the app is offline. Click to save changes to local storage.
 - The CRF save button when CRF changes have been saved successfully to the study database, while online.
- The CRF save button when CRF changes have been saved successfully to the study database, while online.
 - The CRF save button when CRF changes have been saved successfully to local storage, while offline. The changes must still be uploaded to the study database once back online.
- The CRF save button when CRF changes have been saved successfully to local storage, while offline. The changes must still be uploaded to the study database once back online.
![]() - The CRF save button when the CRF is read only due to being locked by another user.
- The CRF save button when the CRF is read only due to being locked by another user.
 - The CRF save button when the CRF is read only based on user permissions.
- The CRF save button when the CRF is read only based on user permissions.
![]() - CRF conflict. Click to open the list of conflicts between data in local storage and data on the server.
- CRF conflict. Click to open the list of conflicts between data in local storage and data on the server.
 - Field help icon on the data entry form. Click to display the field help information.
- Field help icon on the data entry form. Click to display the field help information.
 - Date picker icon on the data entry form. Click to open the calendar and select a date for the current field.
- Date picker icon on the data entry form. Click to open the calendar and select a date for the current field.
 - Required icon on the data entry form, indicating that the current field must be completed.
- Required icon on the data entry form, indicating that the current field must be completed.
 - Query icon. Click to open the Query dialog for the current field. The icon will change color based on query status: blue (outstanding), orange (pending), or green (resolved). In addition, a small grey circle will indicate the number of queries on that field, if one or more queries have been added.
- Query icon. Click to open the Query dialog for the current field. The icon will change color based on query status: blue (outstanding), orange (pending), or green (resolved). In addition, a small grey circle will indicate the number of queries on that field, if one or more queries have been added.
 - Reason icon. Click to open the Reason dialog for the current field. The icon will change color based on reason status: orange (pending), blue (rejected), or green (resolved).
- Reason icon. Click to open the Reason dialog for the current field. The icon will change color based on reason status: orange (pending), blue (rejected), or green (resolved).
 - Missing value icon. Click to open the Missing Value dialog for the current field. The icon will change to green in color if a missing value code has been selected.
- Missing value icon. Click to open the Missing Value dialog for the current field. The icon will change to green in color if a missing value code has been selected.
 - Reply to the query, in the multiple queries dialog (if enabled).
- Reply to the query, in the multiple queries dialog (if enabled).
 - Edit the query, in the multiple queries dialog (if enabled).
- Edit the query, in the multiple queries dialog (if enabled).
 - Delete the query, in the multiple queries dialog (if enabled).
- Delete the query, in the multiple queries dialog (if enabled).
 - Add a new query, in the multiple queries dialog (if enabled).
- Add a new query, in the multiple queries dialog (if enabled).
 - Manage Documents, on the data entry form. The number of attached documents is shown in the red circle. Click to open the Manage Documents dialog.
- Manage Documents, on the data entry form. The number of attached documents is shown in the red circle. Click to open the Manage Documents dialog.
 - Add document, in the Manage Documents dialog. Click to select a document to attach.
- Add document, in the Manage Documents dialog. Click to select a document to attach.
![]() - CRF help, on the data entry form. Click to open the CRF help dialog.
- CRF help, on the data entry form. Click to open the CRF help dialog.
 - Download data to local storage, in the Storage & Syncing dialog. After selecting sites and/or subjects to delete, click to download the data to local storage.
- Download data to local storage, in the Storage & Syncing dialog. After selecting sites and/or subjects to delete, click to download the data to local storage.
 - Submit data to server, in the Storage & Syncing dialog. After selecting site and/or subjects to upload, click to submit the data to the server while online.
- Submit data to server, in the Storage & Syncing dialog. After selecting site and/or subjects to upload, click to submit the data to the server while online.
 - Delete data from local storage, in the Storage & Syncing dialog. After selecting sites and/or subjects to delete, click to remove the data saved to local storage.
- Delete data from local storage, in the Storage & Syncing dialog. After selecting sites and/or subjects to delete, click to remove the data saved to local storage.
 - Subject data has been downloaded to local storage. After download is complete, the date and time of download will appear below the icon.
- Subject data has been downloaded to local storage. After download is complete, the date and time of download will appear below the icon.
 - The downloaded subject data includes attachments.
- The downloaded subject data includes attachments.
![]() - Subject data has been downloaded to local storage, in the Studies and Subjects page.
- Subject data has been downloaded to local storage, in the Studies and Subjects page.
 - Subject data has been downloaded to local storage, in the Sites page. The number inside the grey circle represents the number of subjects with data downloaded to local storage.
- Subject data has been downloaded to local storage, in the Sites page. The number inside the grey circle represents the number of subjects with data downloaded to local storage.
![]() - Subject data has not been downloaded to local storage, in the Subjects page. Click to select that subject to download if online.
- Subject data has not been downloaded to local storage, in the Subjects page. Click to select that subject to download if online.
![]() - The subject has been selected for download on the Subjects page but has not been downloaded yet.
- The subject has been selected for download on the Subjects page but has not been downloaded yet.
 - New subject data entered while offline is saved to local storage and not yet submitted to the server.
- New subject data entered while offline is saved to local storage and not yet submitted to the server.
 - Subject data changes entered while offline are saved to local storage and not yet submitted to the server.
- Subject data changes entered while offline are saved to local storage and not yet submitted to the server.
 - Data conflict, indicating that at least one data record has a conflict that must be resolved before submitting data to the server.
- Data conflict, indicating that at least one data record has a conflict that must be resolved before submitting data to the server.
Table of Contents
On the Subjects page, click a subject ID from the list to open the subject binder page.
If the subject ID you need is not in the list, click
 to add a new subject ID.
This opens a dialog with two text input fields. Enter the subject ID to add to the current site. Confirm the subject ID by entering it again. Click to confirm the subject creation, or to close the dialog without creating a subject.
to add a new subject ID.
This opens a dialog with two text input fields. Enter the subject ID to add to the current site. Confirm the subject ID by entering it again. Click to confirm the subject creation, or to close the dialog without creating a subject.
The subject binder page displays the available visits for that
subject. Under each visit, the CRFs available at that visit are presented.
Click a visit
to see the list of CRFs in that visit. To begin data entry,
select the appropriate visit and CRF. To change to a different visit or CRF,
click
 in the CRF page header area to return to the subject binder page.
in the CRF page header area to return to the subject binder page.
The last in-focused field displays a vertical bar on the left edge of the field. It may contain color information, including red (required and missing or illegal values), blue (outstanding query), green (resolved), orange (pending), and black (otherwise).
Some fields only accept specific data formats. Field formatting is shown in the blank field to help guide data entry. For example, a date field may have the format YYYY/MM/DD
or a lab result field may have the format nn.nn.
Some fields may have legal ranges defined. If you enter an illegal value, the value turns red, and you are shown a warning similar to: "Input value is not in the legal range." The warning disappears after a few seconds, though the value remains red until corrected.
In addition to the description for each field on the CRF, help information may be available for the field. This is indicated with a
 icon. Click
icon. Click
 to view the help message.
to view the help message.
Keyboard navigation on DFcollect is not standardized on tablet devices, hence field skipping is not implemented. Navigate directly to fields by selecting them.
Numeric digits (0-9), and a sign symbol (+ or -) can be entered in number fields. If a decimal or other character is required, it is entered automatically to match the required format for the field.
Except for the | character,
any text may be entered in a string field. A maximum field length may be defined which limits the number of characters that can be entered.
Use the date picker to select a date. If a date is entered using the keyboard, it must follow the defined format, e.g. DD-MMM-YYYY, YYYY/MM/DD, DDMMYY. Partial dates may only be entered via the keyboard.
Only one response option can be selected for each choice field. The field is displayed as radio buttons if there are three or fewer response options, otherwise they are displayed in a drop-down menu. To clear a response on a radio button, click the currently selected radio button again. Drop-down menus show the empty response as the first option - use that to clear the response.
A check field can be checked or unchecked. Multiple check fields may be included in one item; check all that apply.
Select a point along the scale by clicking that point. Drag the slider to select values more precisely. The selected value is shown above the scale in the middle, with the low and high limits of the scale shown on the left and right respectively. To remove the value, click , select from the dropdown, and click .
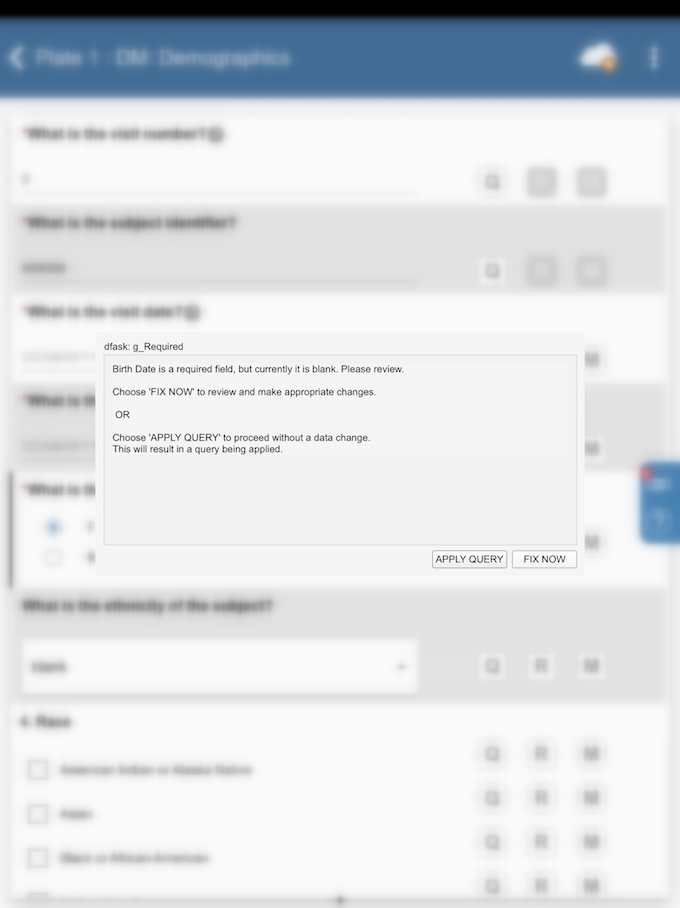
Edit checks are defined during study setup. They are fragments of logic that enforce study expectations for the data collected. They run interactively during data entry and data review. Edit checks may be run when you enter a CRF or a field, or when you leave a CRF or a field. Edit checks perform various actions, such as displaying a warning message, adding a query, calculating data, or changing data to view only.
The following is an example edit check. Your own study will likely have similar edit checks that also display messages and request input. In the edit check example shown below, the edit check has detected an inconsistency in the response. The user is asked to click to return to the data field to make a correction, or click to add a query to the field and fix the problem later.
When you have completed data entry on a CRF, you must save your changes before
leaving the CRF. To do so, click
 if you are online, or
if you are online, or
 if you are offline, which are located in the Header Panel.
If you are offline,
you must remember to upload the changes to the server when you connect to a network.
More details on this process, including handling conflicts, can be found in
Working Offline.
if you are offline, which are located in the Header Panel.
If you are offline,
you must remember to upload the changes to the server when you connect to a network.
More details on this process, including handling conflicts, can be found in
Working Offline.
If you leave the CRF before saving, the following dialog is presented:
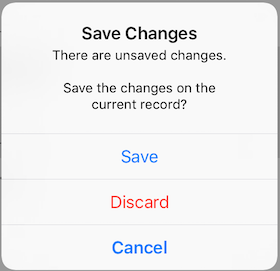
Click to remain on the CRF. Click to save your changes before leaving, or click to discard the data on the CRF. If you discard the data, your changes are not saved and cannot be retrieved.
To return to the Subjects list from a subject binder or CRF, click
 until you arrive at the Subjects list.
until you arrive at the Subjects list.
To search for a specific subject ID, click
 to open the search bar. Type the subject ID into the search bar and click
to open the search bar. Type the subject ID into the search bar and click
 .
You are taken to the first subject ID in the list that matches your search.
Click
.
You are taken to the first subject ID in the list that matches your search.
Click
 and
and
 to move to the next or the previous subject IDs that match your search.
Clicking
to move to the next or the previous subject IDs that match your search.
Clicking
 takes you back to the first subject ID in the list that matches the search.
takes you back to the first subject ID in the list that matches the search.
Table of Contents
Queries are used to request corrections or clarifications about the data. There are four query dialogs: Add Query, Edit Query, Reply to Query, and Delete Query. The following sections explain in detail how to use these dialogs.
For studies where multiple queries per field are enabled, there is an additional dialog where users can add a new query or choose an existing query to reply to, edit, or delete. Further details are provided in Multiple Queries Dialog.
To add a query to a field, click . If there is no query on a field, the Add Query dialog opens. Select an appropriate category from the dropdown menu, and provide the query detail in the provided text field. Once complete, click to add a query to the field.
To edit a query, click . If the query is resolved, the Edit Query dialog opens. Otherwise, the Reply to Query dialog opens. Click , and the Edit Query dialog opens. Select an appropriate category and status from the dropdown menu, and provide the query detail in the provided text field. Once complete, click to finish editing the query.
If a query is already resolved, it cannot be replied to. Otherwise, to reply to an outstanding query on a field, click . The Reply to Query dialog opens, displaying the query detail. Enter the query reply content in the provided text field. Once complete, click .
Queries are rarely deleted. Once a query is created, it should be resolved, perhaps as irrelevant.
If it is necessary to delete an existing query, click . If the query is outstanding or pending, the Reply to Query dialog opens. Click , and the Edit Query dialog opens. Click , the Delete Query dialog opens. In the Delete Query dialog, click to confirm deletion of the query on the field. At each step please ensure that the query really should be deleted.
In a study with multiple queries per field enabled, click for a field with an existing query to see the multiple queries dialog:
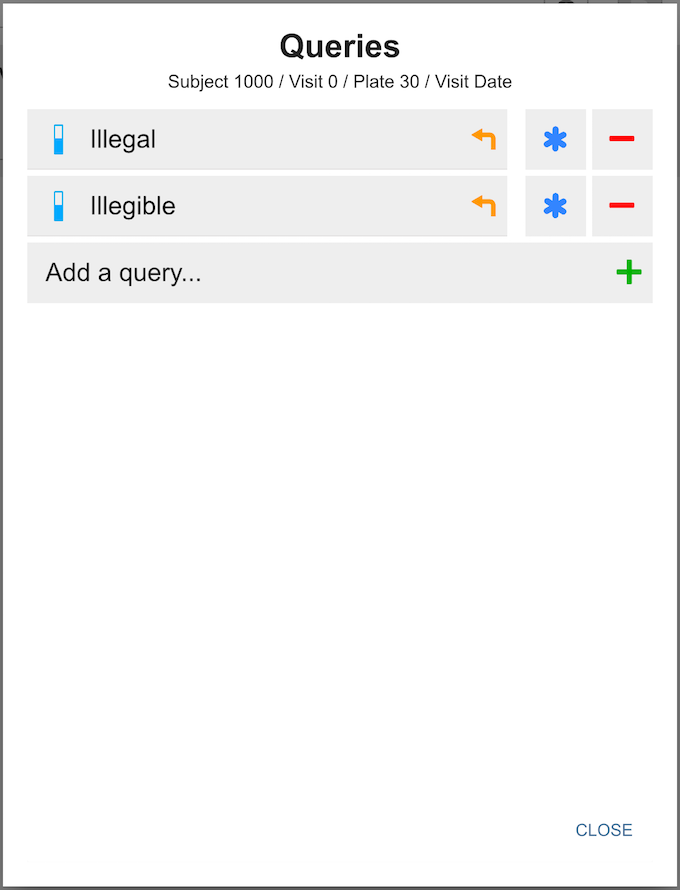
The icons used in the multiple queries dialog are:
-
 Reply
Reply
-
 Edit
Edit
-
 Delete
Delete
-
 Add
Add
In single query per field studies there are navigation buttons at the bottom of each dialog to navigate from one dialog to another. These are not present in studies that permit multiple queries per field. Instead, the multiple query-enabled study query dialogs have a back arrow at the left top corner. The back arrow returns you to the Multiple Queries dialog.
Reasons are a way to provide additional information about existing data or to explain why data is changed. For each data field, the user can add a new reason or edit an existing reason using the Reason for Data Value dialog.
To add a reason to a field, click next to the field. The Reason for Data Value dialog opens. Select an appropriate status from the dropdown menu and enter the reason detail in the provided text field. Click to add the reason to the field.
In some cases, the Reason for Data Value dialog may open automatically when a data value is changed. In these cases, a reason is required before the data change is accepted. If the data change was made in error, click in the Add Reason dialog to discard the data change.
To edit an existing reason, click to open the Reason for Data Value dialog. Change the reason status and/or detail and click to finish editing and close the dialog.
To delete an existing reason, click to open the Reason for Data Value dialog. Click and then click to confirm that the reason should be deleted.
Missing value codes provide a way to mark a data value as missing. Users may select a missing value code for any data field that is not essential to indicate that the data value will not be entered.
To mark a data value as missing, click next to the input field. The Missing Value dialog opens. Select an appropriate missing value code from the dropdown menu, and click to finish.
After marking a data value as missing, the field value is set to the missing value code and the field is disabled. Disabled fields can still be tabbed to, however editing the field is not possible.
To enter data in a field that has previously been marked as missing, click . In the Missing Value dialog, select the option from the dropdown menu, and click to finish. This enables the field for data entry and resets the field value to blank.
Queries can also be resolved via .
Click , and then click for the query that is to be resolved. Select an appropriate Status from the dropdown menu, and optionally supply Detail and Note information in the respective text areas. Once complete, click to resolve the query.
DFcollect allows users to attach documents to a CRF, which accommodates adding more data and information in other formats. This can be useful for managing images, or other recordings, that are relevant to the data of the current CRF.
DFcollect allows users to upload, view and download PDFs, images, audio, and video. Specifically for images, DFcollect supports JPEG (JPG), PNG, and BMP formats; for audio, DFcollect supports MP3, and WAV formats; for video, DFcollect supports MP4, and AVI formats.
Click  in
the CRF Menu to open the Manage Documents view.
The number with red background
in
the CRF Menu to open the Manage Documents view.
The number with red background  indicates the number of existing documents for this CRF.
indicates the number of existing documents for this CRF.
The Manage Documents view is as below:
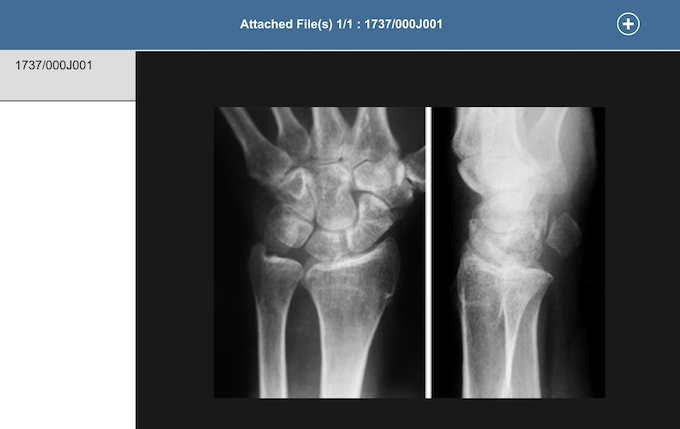
By default, the first document, if any, is opened for review. To view another document, click the tab matching the document name that you want to open.
Many document types can be previewed directly, including PDF, JPEG (JPG), PNG, and MP4 format. Other formats can be downloaded to the local computer and viewed using appropriate 'helper' software.
Click  in the header of Manage Documents view to open the file browser and select one file, after which the Attach File confirmation
dialog appears. Click to confirm and add the file, or to cancel the action.
in the header of Manage Documents view to open the file browser and select one file, after which the Attach File confirmation
dialog appears. Click to confirm and add the file, or to cancel the action.
![[Note]](../../imagedata/note.png) | Note |
|---|---|
For iOS® users, if Optimize Storage is enabled on your device, iCloud Photos automatically manages the size of your photo library on your device. Your original photos and videos are stored in iCloud and space-saving versions are kept on your device. Turn on the "Download and keep originals" setting on your device in order to have your original photos and videos available to be uploaded to DFcollect. |
Table of Contents
If you are planning to view, enter, or modify data while not connected to the internet (offline), you must in advance, while connected to the internet, download the data to local storage on your device.
There are two ways to download data to local storage. The first way is from the Storage & Syncing page, accessed via the application menu. The second is from the Subjects page.
Log in to DFcollect while online. Navigate to the study you
intend to work with offline,
click  to open the Application Menu, and select from the dropdown menu. This displays the list of sites and subjects you have access to and whether they have been downloaded to local storage.
to open the Application Menu, and select from the dropdown menu. This displays the list of sites and subjects you have access to and whether they have been downloaded to local storage.
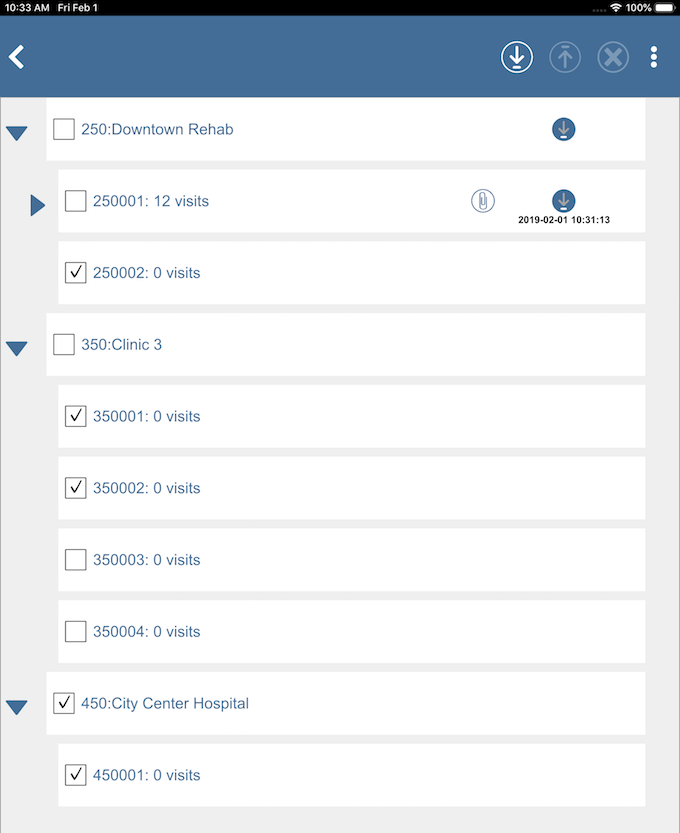
You select the sites or subjects to download by clicking the checkbox in front of the site number or subject ID.
Click  to expand a site or a subject. You can also expand the subjects and visits if they have been downloaded to local storage. Click
to expand a site or a subject. You can also expand the subjects and visits if they have been downloaded to local storage. Click  to collapse the expanded items.
to collapse the expanded items.
After identifying the site(s) and/or subject(s) to download,
click  to start the download to local storage.
A Download Progress dialog opens while the download is in progress and closes automatically when complete.
to start the download to local storage.
A Download Progress dialog opens while the download is in progress and closes automatically when complete.
The data are now available to view and modify while offline.
![[Important]](../../imagedata/important.png) | Store only the data needed |
|---|---|
|
While it can be tempting to include all of the permitted sites and subjects in local storage, this is not recommended. Depending upon the network speed, it can take a considerable amount of time to download the requested subjects and attached documents. It will also require local storage in which to keep the downloaded content. Finally, when you are online again, a comparison must be done against each record in local storage to determine if it needs to be uploaded, and if yes, to upload it again. It is far more efficient to download only the subjects or sites that you will require while working offline. |
The icon  to the right of a site name indicates this site has downloaded data in local storage. The
to the right of a site name indicates this site has downloaded data in local storage. The  icon to the right of the subject ID indicates that it has been downloaded, and includes the date and time it was downloaded. The
icon to the right of the subject ID indicates that it has been downloaded, and includes the date and time it was downloaded. The  icon next to the subject ID indicates this subject also has documents downloaded.
icon next to the subject ID indicates this subject also has documents downloaded.
The Studies, Sites, and Subjects pages also indicate which data has been downloaded to local storage. The icon to the right of the subject ID is updated to show  . The same icon is displayed in the Studies page. In the Sites page the same icon is also displayed along with the number of subjects downloaded.
. The same icon is displayed in the Studies page. In the Sites page the same icon is also displayed along with the number of subjects downloaded.
To refresh existing downloaded data, repeat the above steps to re-download.
Log in to DFcollect while online. Navigate to the study and
site of interest.
Click ![]() to the right of the subject ID to select that
subject for download.
The download icon updates to
to the right of the subject ID to select that
subject for download.
The download icon updates to
![]() indicating that the subject is selected for download.
You may select multiple subjects at a time.
Then click
indicating that the subject is selected for download.
You may select multiple subjects at a time.
Then click  in the header to start downloading the selected subjects. The number in the header to the left of the header download button indicates the number of subjects chosen to download. Once downloaded, the icon to the right of
each subject ID is updated to
in the header to start downloading the selected subjects. The number in the header to the left of the header download button indicates the number of subjects chosen to download. Once downloaded, the icon to the right of
each subject ID is updated to  .
The same icon is displayed in the Studies page. In the Sites page the same icon will also be displayed along with the number of subjects downloaded.
.
The same icon is displayed in the Studies page. In the Sites page the same icon will also be displayed along with the number of subjects downloaded.
To refresh existing downloaded subject data, repeat the above steps to re-download.
To use DFcollect offline, you can simply login while not connected to the internet, or you can set DFcollect to be offline even if you are connected to the internet (Wi-Fi or cellular).
To set DFcollect to be offline, on the login page, click  and select . Slide Server Connection to the left (off). After logging in, you will see a red line across the top of the page to indicate that you are offline.
and select . Slide Server Connection to the left (off). After logging in, you will see a red line across the top of the page to indicate that you are offline.
If you leave Server Connection on but are not connected to the internet while in DFcollect, the Save button in the header of the CRF will display as  to indicate that you are offline.
to indicate that you are offline.
After data have been downloaded to local storage, the process of data entry is the same while offline as it is while online,
except for how data is saved.
Instead of being saved to the server, the data is saved to local storage on your device, shown by  in the header of the CRF.
in the header of the CRF.
When a CRF is saved successfully offline, in the visits and plates page, there is an additional  icon next to a plate (when the visit is expanded) or next a visit (when the visit is collapsed). Likewise, the
icon next to a plate (when the visit is expanded) or next a visit (when the visit is collapsed). Likewise, the  icon also appears in the Subjects and Sites page. When data for a new subject is added while offline, in the Subjects page you will see
icon also appears in the Subjects and Sites page. When data for a new subject is added while offline, in the Subjects page you will see  along with the
along with the  icon next to the newly created subject. Once you are back online, the data must be submitted to the server.
icon next to the newly created subject. Once you are back online, the data must be submitted to the server.
To submit data to the server that was entered while offline,
click  in the page header and select . In this view, you select the subjects or sites you want to upload
(generally this would be all of them),
then click
in the page header and select . In this view, you select the subjects or sites you want to upload
(generally this would be all of them),
then click  to submit data to server.
An Upload Progress dialog appears
while the upload is in progress and closes automatically when complete. The
to submit data to server.
An Upload Progress dialog appears
while the upload is in progress and closes automatically when complete. The  icon will no longer appear next to that subject and site, confirming
that the data has been saved on the server.
icon will no longer appear next to that subject and site, confirming
that the data has been saved on the server.
A data conflict may occur if there were changes made to data
on the server after data were downloaded to local storage,
and then inconsistent changes are submitted back to the server
from local storage.
Conflicts must be resolved by either verifying that the server values
are correct or submitting the local storage values to the server.
Conflicts are indicated by a  .
.
To resolve the conflict, open the CRF with the conflict and click ![]() in the header of the CRF to display the Conflict details. Review the conflicts listed and click or to indicate which data to keep,
and then click to submit the data to the server.
in the header of the CRF to display the Conflict details. Review the conflicts listed and click or to indicate which data to keep,
and then click to submit the data to the server.
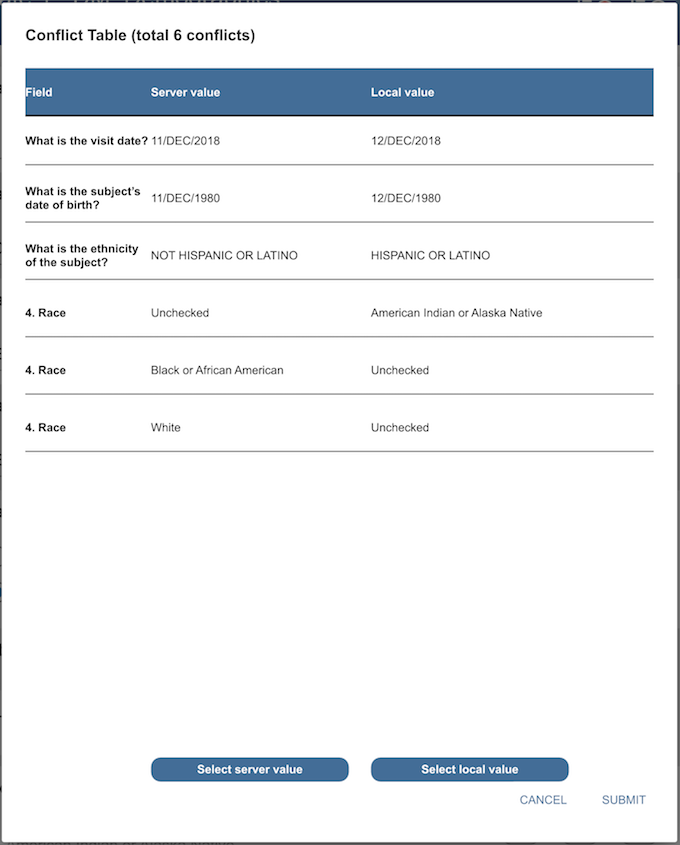
If the local value is selected, the fields with changed data will have a pending reason attached automatically to indicate the data change. The reason detail shows both server and local data value. If the server value is selected, the data on the server will not change and no reasons will be added.
Data in local storage is not automatically deleted after it is submitted. Instead it must be explicitly deleted. Before deleting, ensure that all local changes have been successfully submitted to the server.
To delete data from local storage,
click  in the page header and select .
Select the site(s) and/or subject(s) to delete, click
in the page header and select .
Select the site(s) and/or subject(s) to delete, click  in the header, and click when prompted. The data will no longer be available offline.
in the header, and click when prompted. The data will no longer be available offline.
If subject data has been added or modified while offline and not yet submitted to the server, it must be submitted before you delete it from local storage. If you forget to do this and try to delete the data in local storage, you are notified that you are deleting records from storage that have not been submitted to the study server.
![[Important]](../../imagedata/important.png) | Submit all offline data before deleting |
|---|---|
|
If you click , you are choosing to ignore the warning and the data saved to local storage will be lost. This might be useful if you are testing, or performing training, and the test data should not be saved centrally. But this is an uncommon situation. In general, you must ensure that all locally stored data is submitted before it is deleted. |
Click to cancel deleting the data from local storage.
Table of Contents
- A.1. External Software Copyrights
- A.1.1. DCMTK software package
- A.1.2. Jansson License
- A.1.3. HylaFAX Facsimile Software
- A.1.4. Mimencode
- A.1.5. RSA Data Security, Inc., MD5 message-digest algorithm
- A.1.6. mpack/munpack
- A.1.7. TIFF
- A.1.8. PostgreSQL
- A.1.9. OpenSSL License
- A.1.10. Original SSLeay License
- A.1.11. gawk
- A.1.12. Ghostscript
- A.1.13. MariaDB and FreeTDS
- A.1.14. QtAV
- A.1.15. FFmpeg
- A.1.16. c3.js
- A.1.17. d3.js
DFdiscover software uses several third-party software components as part of its server side and/or client tools.
The copyright information for each is provided below. If you would like to receive source codes of these third-party components, please send us your request at <support@datafax.com>.
Copyright Copyright © 1994-2011, OFFIS e.V. All rights reserved.
This software and supporting documentation were developed by
OFFIS e.V.
R&D Division Health
Eschereg 2
26121 Oldenburg, Germany
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
Neither the name of OFFIS nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Copyright Copyright © 2009-2014 Petri Lehtinen <petri&digip.org>
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Copyright Copyright © 1990-1996 Sam Leffler Copyright Copyright © 1991-1996 Silicon Graphics, Inc. HylaFAX is a trademark of Silicon Graphics, Inc.
Permission to use, copy, modify, distribute, and sell this software and its documentation for any purpose is hereby granted without fee, provided that (i) the above copyright notices and this permission notice appear in all copies of the software and related documentation, and (ii) the names of Sam Leffler and Silicon Graphics may not be used in any advertising or publicity relating to the software without the specific, prior written permission of Sam Leffler and Silicon Graphics.
THE SOFTWARE IS PROVIDED “AS-IS” AND WITHOUT WARRANTY OF ANY KIND, EXPRESS, IMPLIED OR OTHERWISE, INCLUDING WITHOUT LIMITATION, ANY WARRANTY OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. IN NO EVENT SHALL SAM LEFFLER OR SILICON GRAPHICS BE LIABLE FOR ANY SPECIAL, INCIDENTAL, INDIRECT OR CONSEQUENTIAL DAMAGES OF ANY KIND, OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER OR NOT ADVISED OF THE POSSIBILITY OF DAMAGE, AND ON ANY THEORY OF LIABILITY, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
Copyright Copyright © 1991 Bell Communications Research, Inc. (Bellcore)
Permission to use, copy, modify, and distribute this material for any purpose and without fee is hereby granted, provided that the above copyright notice and this permission notice appear in all copies, and that the name of Bellcore not be used in advertising or publicity pertaining to this material without the specific, prior written permission of an authorized representative of Bellcore. BELLCORE MAKES NO REPRESENTATIONS ABOUT THE ACCURACY OR SUITABILITY OF THIS MATERIAL FOR ANY PURPOSE. IT IS PROVIDED “AS IS”, WITHOUT ANY EXPRESS OR IMPLIED WARRANTIES.
Copyright Copyright © 1991-2, RSA Data Security, Inc. Created 1991. All rights reserved. License to copy and use this software is granted provided that it is identified as the “RSA Data Security, Inc. MD5 Message-Digest Algorithm” in all material mentioning or referencing this software or this function. License is also granted to make and use derivative works provided that such works are identified as “derived from the RSA Data Security, Inc. MD5 Message-Digest Algorithm” in all material mentioning or referencing the derived work. RSA Data Security, Inc. makes no representations concerning either the merchantability of this software or the suitability of this software for any particular purpose. It is provided “as is” without express or implied warranty of any kind. These notices must be retained in any copies of any part of this documentation and/or software.
Copyright © Copyright 1993,1994 by Carnegie Mellon University All Rights Reserved.
Permission to use, copy, modify, distribute, and sell this software and its documentation for any purpose is hereby granted without fee, provided that the above copyright notice appear in all copies and that both that copyright notice and this permission notice appear in supporting documentation, and that the name of Carnegie Mellon University not be used in advertising or publicity pertaining to distribution of the software without specific, written prior permission. Carnegie Mellon University makes no representations about the suitability of this software for any purpose. It is provided “as is” without express or implied warranty.
CARNEGIE MELLON UNIVERSITY DISCLAIMS ALL WARRANTIES WITH REGARD TO THIS SOFTWARE, INCLUDING ALL IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS, IN NO EVENT SHALL CARNEGIE MELLON UNIVERSITY BE LIABLE FOR ANY SPECIAL, INDIRECT OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER IN AN ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
Copyright Copyright © 1988-1997 Sam Leffler Copyright Copyright © 1991-1997 Silicon Graphics, Inc.
Permission to use, copy, modify, distribute, and sell this software and its documentation for any purpose is hereby granted without fee, provided that (i) the above copyright notices and this permission notice appear in all copies of the software and related documentation, and (ii) the names of Sam Leffler and Silicon Graphics may not be used in any advertising or publicity relating to the software without the specific, prior written permission of Sam Leffler and Silicon Graphics.
THE SOFTWARE IS PROVIDED “AS-IS” AND WITHOUT WARRANTY OF ANY KIND, EXPRESS, IMPLIED OR OTHERWISE, INCLUDING WITHOUT LIMITATION, ANY WARRANTY OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. IN NO EVENT SHALL SAM LEFFLER OR SILICON GRAPHICS BE LIABLE FOR ANY SPECIAL, INCIDENTAL, INDIRECT OR CONSEQUENTIAL DAMAGES OF ANY KIND, OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER OR NOT ADVISED OF THE POSSIBILITY OF DAMAGE, AND ON ANY THEORY OF LIABILITY, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
Copyright © 1996-2014 by the PostgreSQL Global Development Group and is distributed under the terms of the license of the University of California below.
Postgres95 is Copyright © 1994-5 by the Regents of the University of California.
Permission to use, copy, modify, and distribute this software and its documentation for any purpose, without fee, and without a written agreement is hereby granted, provided that the above copyright notice and this paragraph and the following two paragraphs appear in all copies.
IN NO EVENT SHALL THE UNIVERSITY OF CALIFORNIA BE LIABLE TO ANY PARTY FOR DIRECT, INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAMAGES, INCLUDING LOST PROFITS, ARISING OUT OF THE USE OF THIS SOFTWARE AND ITS DOCUMENTATION, EVEN IF THE UNIVERSITY OF CALIFORNIA HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. THE UNIVERSITY OF CALIFORNIA SPECIFICALLY DISCLAIMS ANY WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE SOFTWARE PROVIDED HEREUNDER IS ON AN “AS-IS” BASIS, AND THE UNIVERSITY OF CALIFORNIA HAS NO OBLIGATIONS TO PROVIDE MAINTENANCE, SUPPORT, UPDATES, ENHANCEMENTS, OR MODIFICATIONS.
Copyright Copyright © 1998-2016 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
All advertising materials mentioning features or use of this software must display the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in .the OpenSSL Toolkit.” (http://www.openssl.org/)
The names “OpenSSL Toolkit” and "OpenSSL Project" must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact openssl-core@openssl.org.
Products derived from this software may not be called “OpenSSL” nor may “OpenSSL” appear in their names without prior written permission of the OpenSSL Project.
Redistributions of any form whatsoever must retain the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit. (http://www.openssl.org)”
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS” AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (<eay@cryptsoft.com>). This product includes software written by Tim Hudson (<tjh@cryptsoft.com>).
Copyright Copyright © 1995-1998 Eric Young (<eay@cryptsoft.com>)
All rights reserved.
This package is an SSL implementation written
by Eric Young (<eay@cryptsoft.com>).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as
the following conditions are aheared to. The following conditions
apply to all code found in this distribution, be it the RC4, RSA,
lhash, DES, etc., code; not just the SSL code. The SSL documentation
included with this distribution is covered by the same copyright terms
except that the holder is Tim Hudson (<tjh@cryptsoft.com>).
Copyright remains Eric Young's, and as such any Copyright notices in the code are not to be removed. If this package is used in a product, Eric Young should be given attribution as the author of the parts of the library used. This can be in the form of a textual message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
-
Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
All advertising materials mentioning features or use of this software must display the following acknowledgement: “This product includes cryptographic software written by Eric Young (
<eay@cryptsoft.com>)” The word “cryptographic” can be left out if the rouines from the library being used are not cryptographic related :-).If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: “This product includes software written by Tim Hudson (
<tjh@cryptsoft.com>)”
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The licence and distribution terms for any publically available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and put under another distribution licence [including the GNU Public Licence.]
GNU GENERAL PUBLIC LICENSE Version 2, June 1991
http://www.gnu.org/licenses/gpl-2.0.html
Copyright Copyright © 1989, 1991 Free Software Foundation, Inc.
51 Franklin Street, Fifth Floor,
Boston, MA 02110-1301, USA
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
The licenses for most software are designed to take away your freedom to share and change it. By contrast, the GNU General Public License is intended to guarantee your freedom to share and change free software--to make sure the software is free for all its users. This General Public License applies to most of the Free Software Foundation's software and to any other program whose authors commit to using it. (Some other Free Software Foundation software is covered by the GNU Lesser General Public License instead.) You can apply it to your programs, too.
When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are designed to make sure that you have the freedom to distribute copies of free software (and charge for this service if you wish), that you receive source code or can get it if you want it, that you can change the software or use pieces of it in new free programs; and that you know you can do these things.
To protect your rights, we need to make restrictions that forbid anyone to deny you these rights or to ask you to surrender the rights. These restrictions translate to certain responsibilities for you if you distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must give the recipients all the rights that you have. You must make sure that they, too, receive or can get the source code. And you must show them these terms so they know their rights.
We protect your rights with two steps: (1) copyright the software, and (2) offer you this license which gives you legal permission to copy, distribute and/or modify the software.
Also, for each author's protection and ours, we want to make certain that everyone understands that there is no warranty for this free software. If the software is modified by someone else and passed on, we want its recipients to know that what they have is not the original, so that any problems introduced by others will not reflect on the original authors' reputations.
Finally, any free program is threatened constantly by software patents. We wish to avoid the danger that redistributors of a free program will individually obtain patent licenses, in effect making the program proprietary. To prevent this, we have made it clear that any patent must be licensed for everyone's free use or not licensed at all.
The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
This License applies to any program or other work which contains a notice placed by the copyright holder saying it may be distributed under the terms of this General Public License. The “Program”, below, refers to any such program or work, and a “work based on the Program” means either the Program or any derivative work under copyright law: that is to say, a work containing the Program or a portion of it, either verbatim or with modifications and/or translated into another language. (Hereinafter, translation is included without limitation in the term “modification”.) Each licensee is addressed as “you”.
Activities other than copying, distribution and modification are not covered by this License; they are outside its scope. The act of running the Program is not restricted, and the output from the Program is covered only if its contents constitute a work based on the Program (independent of having been made by running the Program). Whether that is true depends on what the Program does.
You may copy and distribute verbatim copies of the Program's source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on each copy an appropriate copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the absence of any warranty; and give any other recipients of the Program a copy of this License along with the Program.
You may charge a fee for the physical act of transferring a copy, and you may at your option offer warranty protection in exchange for a fee.
You may modify your copy or copies of the Program or any portion of it, thus forming a work based on the Program, and copy and distribute such modifications or work under the terms of Section 1 above, provided that you also meet all of these conditions:
You must cause the modified files to carry prominent notices stating that you changed the files and the date of any change.
-
You must cause any work that you distribute or publish, that in whole or in part contains or is derived from the Program or any part thereof, to be licensed as a whole at no charge to all third parties under the terms of this License.
If the modified program normally reads commands interactively when run, you must cause it, when started running for such interactive use in the most ordinary way, to print or display an announcement including an appropriate copyright notice and a notice that there is no warranty (or else, saying that you provide a warranty) and that users may redistribute the program under these conditions, and telling the user how to view a copy of this License. (Exception: if the Program itself is interactive but does not normally print such an announcement, your work based on the Program is not required to print an announcement.) These requirements apply to the modified work as a whole. If identifiable sections of that work are not derived from the Program, and can be reasonably considered independent and separate works in themselves, then this License, and its terms, do not apply to those sections when you distribute them as separate works. But when you distribute the same sections as part of a whole which is a work based on the Program, the distribution of the whole must be on the terms of this License, whose permissions for other licensees extend to the entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your rights to work written entirely by you; rather, the intent is to exercise the right to control the distribution of derivative or collective works based on the Program.
In addition, mere aggregation of another work not based on the Program with the Program (or with a work based on the Program) on a volume of a storage or distribution medium does not bring the other work under the scope of this License.
You may copy and distribute the Program (or a work based on it, under Section 2) in object code or executable form under the terms of Sections 1 and 2 above provided that you also do one of the following:
Accompany it with the complete corresponding machine-readable source code, which must be distributed under the terms of Sections 1 and 2 above on a medium customarily used for software interchange; or,
-
Accompany it with a written offer, valid for at least three years, to give any third party, for a charge no more than your cost of physically performing source distribution, a complete machine-readable copy of the corresponding source code, to be distributed under the terms of Sections 1 and 2 above on a medium customarily used for software interchange; or,
-
Accompany it with the information you received as to the offer to distribute corresponding source code. (This alternative is allowed only for noncommercial distribution and only if you received the program in object code or executable form with such an offer, in accord with Subsection b above.) The source code for a work means the preferred form of the work for making modifications to it. For an executable work, complete source code means all the source code for all modules it contains, plus any associated interface definition files, plus the scripts used to control compilation and installation of the executable. However, as a special exception, the source code distributed need not include anything that is normally distributed (in either source or binary form) with the major components (compiler, kernel, and so on) of the operating system on which the executable runs, unless that component itself accompanies the executable.
If distribution of executable or object code is made by offering access to copy from a designated place, then offering equivalent access to copy the source code from the same place counts as distribution of the source code, even though third parties are not compelled to copy the source along with the object code.
You may not copy, modify, sublicense, or distribute the Program except as expressly provided under this License. Any attempt otherwise to copy, modify, sublicense or distribute the Program is void, and will automatically terminate your rights under this License. However, parties who have received copies, or rights, from you under this License will not have their licenses terminated so long as such parties remain in full compliance.
You are not required to accept this License, since you have not signed it. However, nothing else grants you permission to modify or distribute the Program or its derivative works. These actions are prohibited by law if you do not accept this License. Therefore, by modifying or distributing the Program (or any work based on the Program), you indicate your acceptance of this License to do so, and all its terms and conditions for copying, distributing or modifying the Program or works based on it.
Each time you redistribute the Program (or any work based on the Program), the recipient automatically receives a license from the original licensor to copy, distribute or modify the Program subject to these terms and conditions. You may not impose any further restrictions on the recipients' exercise of the rights granted herein. You are not responsible for enforcing compliance by third parties to this License.
-
If, as a consequence of a court judgment or allegation of patent infringement or for any other reason (not limited to patent issues), conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot distribute so as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not distribute the Program at all. For example, if a patent license would not permit royalty-free redistribution of the Program by all those who receive copies directly or indirectly through you, then the only way you could satisfy both it and this License would be to refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the balance of the section is intended to apply and the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or to contest validity of any such claims; this section has the sole purpose of protecting the integrity of the free software distribution system, which is implemented by public license practices. Many people have made generous contributions to the wide range of software distributed through that system in reliance on consistent application of that system; it is up to the author/donor to decide if he or she is willing to distribute software through any other system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this License.
If the distribution and/or use of the Program is restricted in certain countries either by patents or by copyrighted interfaces, the original copyright holder who places the Program under this License may add an explicit geographical distribution limitation excluding those countries, so that distribution is permitted only in or among countries not thus excluded. In such case, this License incorporates the limitation as if written in the body of this License.
The Free Software Foundation may publish revised and/or new versions of the General Public License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies a version number of this License which applies to it and "any later version", you have the option of following the terms and conditions either of that version or of any later version published by the Free Software Foundation. If the Program does not specify a version number of this License, you may choose any version ever published by the Free Software Foundation.
If you wish to incorporate parts of the Program into other free programs whose distribution conditions are different, write to the author to ask for permission. For software which is copyrighted by the Free Software Foundation, write to the Free Software Foundation; we sometimes make exceptions for this. Our decision will be guided by the two goals of preserving the free status of all derivatives of our free software and of promoting the sharing and reuse of software generally. NO WARRANTY
BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
-
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
The files in the base, psi, lib, toolbin, examples, doc and man directories (folders) and any subdirectories (sub-folders) thereof are part of GPL Ghostscript.
The files in the Resource directory and any subdirectories thereof are also part of GPL Ghostscript, with the explicit exception of the files in the CMap subdirectory (except “Identity-UTF16-H”, which is part of GPL Ghostscript). The CMap files are copyright Adobe Systems Incorporated and covered by a separate, GPL compatible license.
The files under the jpegxr directory and any subdirectories thereof are distributed under a no cost, open source license granted by the ITU/ISO/IEC but it is not GPL compatible - see jpegxr/COPYRIGHT.txt for details.
GPL Ghostscript is free software; you can redistribute it and/or modify it under the terms the GNU General Public License as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version.
GPL Ghostscript is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details.
You should have received a copy of the GNU General Public License along with this program so you can know your rights and responsibilities. It should be in a file named doc/COPYING. If not, write to the
Free Software Foundation, Inc., 59 Temple Place Suite 330, Boston, MA
02111-1307, USA.
GPL Ghostscript contains an implementation of techniques covered by US Patents 5,055,942 and 5,917,614, and corresponding international patents. These patents are licensed for use with GPL Ghostscript under the following grant:
Whereas, Raph Levien (hereinafter “Inventor”) has obtained patent protection for related technology (hereinafter “Patented Technology”), Inventor wishes to aid the the GNU free software project in achieving its goals, and Inventor also wishes to increase public awareness of Patented Technology, Inventor hereby grants a fully paid up, nonexclusive, royalty free license to practice the patents listed below (“the Patents”) if and only if practiced in conjunction with software distributed under the terms of any version of the GNU General Public License as published by the
Free Software Foundation, 59 Temple Place, Suite
330, Boston, MA 02111.
Inventor reserves all other rights, including without limitation, licensing for software not distributed under the GNU General Public License.
5055942 Photographic image reproduction device using digital halftoning to para images allowing adjustable coarseness 5917614 Method and apparatus for error diffusion paraing of images with improved smoothness in highlight and shadow regions
GNU LESSER GENERAL PUBLIC LICENSE Version 2.1, February 1999 http://www.gnu.org/licenses/lgpl-2.1.html
Copyright Copyright © 1991, 1999
Free Software Foundation, Inc.
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
[This is the first released version of the Lesser GPL. It also counts as the successor of the GNU Library Public License, version 2, hence the version number 2.1.]
Preamble The licenses for most software are designed to take away your freedom to share and change it. By contrast, the GNU General Public Licenses are intended to guarantee your freedom to share and change free software--to make sure the software is free for all its users.
This license, the Lesser General Public License, applies to some specially designated software packages--typically libraries--of the Free Software Foundation and other authors who decide to use it. You can use it too, but we suggest you first think carefully about whether this license or the ordinary General Public License is the better strategy to use in any particular case, based on the explanations below.
When we speak of free software, we are referring to freedom of use, not price. Our General Public Licenses are designed to make sure that you have the freedom to distribute copies of free software (and charge for this service if you wish); that you receive source code or can get it if you want it; that you can change the software and use pieces of it in new free programs; and that you are informed that you can do these things.
To protect your rights, we need to make restrictions that forbid distributors to deny you these rights or to ask you to surrender these rights. These restrictions translate to certain responsibilities for you if you distribute copies of the library or if you modify it.
For example, if you distribute copies of the library, whether gratis or for a fee, you must give the recipients all the rights that we gave you. You must make sure that they, too, receive or can get the source code. If you link other code with the library, you must provide complete object files to the recipients, so that they can relink them with the library after making changes to the library and recompiling it. And you must show them these terms so they know their rights.
We protect your rights with a two-step method:
we copyright the library, and
-
we offer you this license, which gives you legal permission to copy, distribute and/or modify the library.
To protect each distributor, we want to make it very clear that there is no warranty for the free library. Also, if the library is modified by someone else and passed on, the recipients should know that what they have is not the original version, so that the original author's reputation will not be affected by problems that might be introduced by others.
Finally, software patents pose a constant threat to the existence of any free program. We wish to make sure that a company cannot effectively restrict the users of a free program by obtaining a restrictive license from a patent holder. Therefore, we insist that any patent license obtained for a version of the library must be consistent with the full freedom of use specified in this license.
Most GNU software, including some libraries, is covered by the ordinary GNU General Public License. This license, the GNU Lesser General Public License, applies to certain designated libraries, and is quite different from the ordinary General Public License. We use this license for certain libraries in order to permit linking those libraries into non-free programs.
When a program is linked with a library, whether statically or using a shared library, the combination of the two is legally speaking a combined work, a derivative of the original library. The ordinary General Public License therefore permits such linking only if the entire combination fits its criteria of freedom. The Lesser General Public License permits more lax criteria for linking other code with the library.
We call this license the "Lesser" General Public License because it does Less to protect the user's freedom than the ordinary General Public License. It also provides other free software developers Less of an advantage over competing non-free programs. These disadvantages are the reason we use the ordinary General Public License for many libraries. However, the Lesser license provides advantages in certain special circumstances.
For example, on rare occasions, there may be a special need to encourage the widest possible use of a certain library, so that it becomes a de-facto standard. To achieve this, non-free programs must be allowed to use the library. A more frequent case is that a free library does the same job as widely used non-free libraries. In this case, there is little to gain by limiting the free library to free software only, so we use the Lesser General Public License.
In other cases, permission to use a particular library in non-free programs enables a greater number of people to use a large body of free software. For example, permission to use the GNU C Library in non-free programs enables many more people to use the whole GNU operating system, as well as its variant, the GNU/Linux operating system.
Although the Lesser General Public License is Less protective of the users' freedom, it does ensure that the user of a program that is linked with the Library has the freedom and the wherewithal to run that program using a modified version of the Library.
The precise terms and conditions for copying, distribution and modification follow. Pay close attention to the difference between a “work based on the library” and a “work that uses the library”. The former contains code derived from the library, whereas the latter must be combined with the library in order to run.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
-
This License Agreement applies to any software library or other program which contains a notice placed by the copyright holder or other authorized party saying it may be distributed under the terms of this Lesser General Public License (also called “this License”). Each licensee is addressed as “you”.
A “library” means a collection of software functions and/or data prepared so as to be conveniently linked with application programs (which use some of those functions and data) to form executables.
The “Library”, below, refers to any such software library or work which has been distributed under these terms. A “work based on the Library” means either the Library or any derivative work under copyright law: that is to say, a work containing the Library or a portion of it, either verbatim or with modifications and/or translated straightforwardly into another language. (Hereinafter, translation is included without limitation in the term “modification”.)
“Source code” for a work means the preferred form of the work for making modifications to it. For a library, complete source code means all the source code for all modules it contains, plus any associated interface definition files, plus the scripts used to control compilation and installation of the library.
Activities other than copying, distribution and modification are not covered by this License; they are outside its scope. The act of running a program using the Library is not restricted, and output from such a program is covered only if its contents constitute a work based on the Library (independent of the use of the Library in a tool for writing it). Whether that is true depends on what the Library does and what the program that uses the Library does.
You may copy and distribute verbatim copies of the Library's complete source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on each copy an appropriate copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the absence of any warranty; and distribute a copy of this License along with the Library.
You may charge a fee for the physical act of transferring a copy, and you may at your option offer warranty protection in exchange for a fee.
You may modify your copy or copies of the Library or any portion of it, thus forming a work based on the Library, and copy and distribute such modifications or work under the terms of Section 1 above, provided that you also meet all of these conditions:
The modified work must itself be a software library.
You must cause the files modified to carry prominent notices stating that you changed the files and the date of any change.
You must cause the whole of the work to be licensed at no charge to all third parties under the terms of this License.
If a facility in the modified Library refers to a function or a table of data to be supplied by an application program that uses the facility, other than as an argument passed when the facility is invoked, then you must make a good faith effort to ensure that, in the event an application does not supply such function or table, the facility still operates, and performs whatever part of its purpose remains meaningful. (For example, a function in a library to compute square roots has a purpose that is entirely well-defined independent of the application. Therefore, Subsection 2d requires that any application-supplied function or table used by this function must be optional: if the application does not supply it, the square root function must still compute square roots.)
These requirements apply to the modified work as a whole. If identifiable sections of that work are not derived from the Library, and can be reasonably considered independent and separate works in themselves, then this License, and its terms, do not apply to those sections when you distribute them as separate works. But when you distribute the same sections as part of a whole which is a work based on the Library, the distribution of the whole must be on the terms of this License, whose permissions for other licensees extend to the entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your rights to work written entirely by you; rather, the intent is to exercise the right to control the distribution of derivative or collective works based on the Library.
In addition, mere aggregation of another work not based on the Library with the Library (or with a work based on the Library) on a volume of a storage or distribution medium does not bring the other work under the scope of this License.
You may opt to apply the terms of the ordinary GNU General Public License instead of this License to a given copy of the Library. To do this, you must alter all the notices that refer to this License, so that they refer to the ordinary GNU General Public License, version 2, instead of to this License. (If a newer version than version 2 of the ordinary GNU General Public License has appeared, then you can specify that version instead if you wish.) Do not make any other change in these notices.
Once this change is made in a given copy, it is irreversible for that copy, so the ordinary GNU General Public License applies to all subsequent copies and derivative works made from that copy.
This option is useful when you wish to copy part of the code of the Library into a program that is not a library.
You may copy and distribute the Library (or a portion or derivative of it, under Section 2) in object code or executable form under the terms of Sections 1 and 2 above provided that you accompany it with the complete corresponding machine-readable source code, which must be distributed under the terms of Sections 1 and 2 above on a medium customarily used for software interchange.
If distribution of object code is made by offering access to copy from a designated place, then offering equivalent access to copy the source code from the same place satisfies the requirement to distribute the source code, even though third parties are not compelled to copy the source along with the object code.
A program that contains no derivative of any portion of the Library, but is designed to work with the Library by being compiled or linked with it, is called a "work that uses the Library". Such a work, in isolation, is not a derivative work of the Library, and therefore falls outside the scope of this License.
However, linking a "work that uses the Library" with the Library creates an executable that is a derivative of the Library (because it contains portions of the Library), rather than a “work that uses the library”. The executable is therefore covered by this License. Section 6 states terms for distribution of such executables.
When a “work that uses the Library” uses material from a header file that is part of the Library, the object code for the work may be a derivative work of the Library even though the source code is not. Whether this is true is especially significant if the work can be linked without the Library, or if the work is itself a library. The threshold for this to be true is not precisely defined by law.
If such an object file uses only numerical parameters, data structure layouts and accessors, and small macros and small inline functions (ten lines or less in length), then the use of the object file is unrestricted, regardless of whether it is legally a derivative work. (Executables containing this object code plus portions of the Library will still fall under Section 6.)
Otherwise, if the work is a derivative of the Library, you may distribute the object code for the work under the terms of Section 6. Any executables containing that work also fall under Section 6, whether or not they are linked directly with the Library itself.
As an exception to the Sections above, you may also combine or link a "work that uses the Library" with the Library to produce a work containing portions of the Library, and distribute that work under terms of your choice, provided that the terms permit modification of the work for the customer's own use and reverse engineering for debugging such modifications.
You must give prominent notice with each copy of the work that the Library is used in it and that the Library and its use are covered by this License. You must supply a copy of this License. If the work during execution displays copyright notices, you must include the copyright notice for the Library among them, as well as a reference directing the user to the copy of this License.
Also, you must do one of these things:
Accompany the work with the complete corresponding machine-readable source code for the Library including whatever changes were used in the work (which must be distributed under Sections 1 and 2 above); and, if the work is an executable linked with the Library, with the complete machine-readable "work that uses the Library", as object code and/or source code, so that the user can modify the Library and then relink to produce a modified executable containing the modified Library. (It is understood that the user who changes the contents of definitions files in the Library will not necessarily be able to recompile the application to use the modified definitions.)
Use a suitable shared library mechanism for linking with the Library. A suitable mechanism is one that
uses at run time a copy of the library already present on the user's computer system, rather than copying library functions into the executable, and
will operate properly with a modified version of the library, if the user installs one, as long as the modified version is interface-compatible with the version that the work was made with.
Accompany the work with a written offer, valid for at least three years, to give the same user the materials specified in Subsection 6a, above, for a charge no more than the cost of performing this distribution.
If distribution of the work is made by offering access to copy from a designated place, offer equivalent access to copy the above specified materials from the same place.
-
Verify that the user has already received a copy of these materials or that you have already sent this user a copy. For an executable, the required form of the “work that uses the Library” must include any data and utility programs needed for reproducing the executable from it. However, as a special exception, the materials to be distributed need not include anything that is normally distributed (in either source or binary form) with the major components (compiler, kernel, and so on) of the operating system on which the executable runs, unless that component itself accompanies the executable.
It may happen that this requirement contradicts the license restrictions of other proprietary libraries that do not normally accompany the operating system. Such a contradiction means you cannot use both them and the Library together in an executable that you distribute.
You may place library facilities that are a work based on the Library side-by-side in a single library together with other library facilities not covered by this License, and distribute such a combined library, provided that the separate distribution of the work based on the Library and of the other library facilities is otherwise permitted, and provided that you do these two things:
Accompany the combined library with a copy of the same work based on the Library, uncombined with any other library facilities. This must be distributed under the terms of the Sections above.
Give prominent notice with the combined library of the fact that part of it is a work based on the Library, and explaining where to find the accompanying uncombined form of the same work.
You may not copy, modify, sublicense, link with, or distribute the Library except as expressly provided under this License. Any attempt otherwise to copy, modify, sublicense, link with, or distribute the Library is void, and will automatically terminate your rights under this License. However, parties who have received copies, or rights, from you under this License will not have their licenses terminated so long as such parties remain in full compliance.
You are not required to accept this License, since you have not signed it. However, nothing else grants you permission to modify or distribute the Library or its derivative works. These actions are prohibited by law if you do not accept this License. Therefore, by modifying or distributing the Library (or any work based on the Library), you indicate your acceptance of this License to do so, and all its terms and conditions for copying, distributing or modifying the Library or works based on it.
Each time you redistribute the Library (or any work based on the Library), the recipient automatically receives a license from the original licensor to copy, distribute, link with or modify the Library subject to these terms and conditions. You may not impose any further restrictions on the recipients' exercise of the rights granted herein. You are not responsible for enforcing compliance by third parties with this License.
If, as a consequence of a court judgment or allegation of patent infringement or for any other reason (not limited to patent issues), conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot distribute so as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not distribute the Library at all. For example, if a patent license would not permit royalty-free redistribution of the Library by all those who receive copies directly or indirectly through you, then the only way you could satisfy both it and this License would be to refrain entirely from distribution of the Library.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the balance of the section is intended to apply, and the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or to contest validity of any such claims; this section has the sole purpose of protecting the integrity of the free software distribution system which is implemented by public license practices. Many people have made generous contributions to the wide range of software distributed through that system in reliance on consistent application of that system; it is up to the author/donor to decide if he or she is willing to distribute software through any other system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this License.
-
If the distribution and/or use of the Library is restricted in certain countries either by patents or by copyrighted interfaces, the original copyright holder who places the Library under this License may add an explicit geographical distribution limitation excluding those countries, so that distribution is permitted only in or among countries not thus excluded. In such case, this License incorporates the limitation as if written in the body of this License.
-
The Free Software Foundation may publish revised and/or new versions of the Lesser General Public License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Library specifies a version number of this License which applies to it and "any later version", you have the option of following the terms and conditions either of that version or of any later version published by the Free Software Foundation. If the Library does not specify a license version number, you may choose any version ever published by the Free Software Foundation.
If you wish to incorporate parts of the Library into other free programs whose distribution conditions are incompatible with these, write to the author to ask for permission. For software which is copyrighted by the Free Software Foundation, write to the Free Software Foundation; we sometimes make exceptions for this. Our decision will be guided by the two goals of preserving the free status of all derivatives of our free software and of promoting the sharing and reuse of software generally.
NO WARRANTY
BECAUSE THE LIBRARY IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE LIBRARY, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE LIBRARY "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE LIBRARY IS WITH YOU. SHOULD THE LIBRARY PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE THE LIBRARY AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE LIBRARY (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE LIBRARY TO OPERATE WITH ANY OTHER SOFTWARE), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
Copyright © Wang Bin <wbsecg1@gmail.com>
Shanghai University->S3 Graphics->Deepin, Shanghai, China
2013-01-21
**QtAV is free software licensed under the term of LGPL v2.1. The player example is licensed under GPL v3. If you use QtAV or its constituent libraries, you must adhere to the terms of the license in question.**
Rather than repeating the text of the LGPL v2.1, the original text can be found in GNU LESSER GENERAL PUBLIC LICENSE, Version 2.1.
Most files in FFmpeg are under the GNU Lesser General Public License version 2.1 or later (LGPL v2.1+). Read the file `COPYING.LGPLv2.1` for details. Some other files have MIT/X11/BSD-style licenses. In combination the LGPL v2.1+ applies to FFmpeg.
Rather than repeating the text of the LGPL v2.1, the original text can be found in GNU LESSER GENERAL PUBLIC LICENSE, Version 2.1.
The MIT License (MIT) Copyright © 2013 Masayuki Tanaka
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Copyright 2010-2017 Mike Bostock All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: * Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer. * Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. * Neither the name of the author nor the names of contributors may be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.