Release 5.1.0
Copyright © 2019 DF/Net Research, Inc.
All rights reserved. No part of this publication may be re-transmitted in any form or by any means, electronic, mechanical, photocopying, recording, or otherwise, without the prior written permission of DF/Net Research, Inc.. Permission is granted for internal re-distribution of this publication by the license holder and their employees for internal use only, provided that the copyright notices and this permission notice appear in all copies.
The information in this document is furnished for informational use only and is subject to change without notice. DF/Net Research, Inc. assumes no responsibility or liability for any errors or inaccuracies in this document or for any omissions from it.
All products or services mentioned in this document are covered by the trademarks, service marks, or product names as designated by the companies who market those products.
Feb 01, 2019
Table of Contents
- Preface
- 1. Introduction
- 2. DFdiscover Software Installation
- 3.
- 4. DFdiscover Configuration
- 5. Integration Testing
- 6. Study Installation
- 7. DFdiscover Acceptance Test Kit (ATK) Installation
- 8. Client Desktop Packages Installation
- 9. Installation Completion
- 10. DFdiscover Installation Worksheet
- 10.1. DFdiscover Software Installation
- 10.1.1. Staffing
- 10.1.2. Before Installation
- 10.1.3. Installation Materials
- 10.1.4. Installation for Linux Systems
- 10.1.5. Migrate User Permissions (upgrade install, from versions older than 3.8, only)
- 10.1.6. Request and Install Server Certificate
- 10.1.7. Request and Install DFdiscover License
- 10.1.8. Migration of pre-2014 studies
- 10.2. HylaFAX Configuration
- 10.3. DFdiscover Configuration
- 10.4. Start DFdiscover
- 10.5. (Re-)configure DFdiscover Master
- 10.6. Configure Incoming and Outgoing Daemons
- 10.7. Integration Testing
- 10.8. Study Installation
- 10.9. DFdiscover Acceptance Test Kit (ATK) Installation
- 10.10. Client Desktop Package Installation
- 10.11. Installation Completion
- 10.12. Completion Sign-off
- A. Copyrights - Acknowledgments
- A.1. External Software Copyrights
- A.1.1. DCMTK software package
- A.1.2. Jansson License
- A.1.3. HylaFAX Facsimile Software
- A.1.4. Mimencode
- A.1.5. RSA Data Security, Inc., MD5 message-digest algorithm
- A.1.6. mpack/munpack
- A.1.7. TIFF
- A.1.8. PostgreSQL
- A.1.9. OpenSSL License
- A.1.10. Original SSLeay License
- A.1.11. gawk
- A.1.12. Ghostscript
- A.1.13. MariaDB and FreeTDS
- A.1.14. QtAV
- A.1.15. FFmpeg
- A.1.16. c3.js
- A.1.17. d3.js
Table of Contents
DF/Net Research, Inc.'s Technical Support Department can be contacted Monday to Friday between 9:00 am and 5:00 pm Eastern Time via any of the following methods:
55 Head Street, Suite 403
Dundas, Ontario L9H 3H8
Telephone: (905) 522-3282
Email: <support@datafax.com>
URL: www.dfnetresearch.com
DF/Net Research, Inc. provides an automated email mailing list for tips, help, and interaction with other DFdiscover users.
To subscribe to the mailing list, complete the simple form found at the DFdiscover User's Group mailing list webpage. It is also possible to unsubscribe from the mailing list by visiting the same webpage.
To submit a message to the mailing list
-
Subscribe to the list. Message submissions are only accepted from members of the list.
-
Create your email message.
-
Send the email message to
<DFUG@datafax.com>.
A number of conventions have been used throughout this document.
Any freestanding sections of code are generally shown like this:
# this is example code code = code + overhead;
If a line starts with # or %, this
character denotes the system prompt and is not typed by the user.
Text may also have several styles:
Emphasized words are shown as follows: emphasized words.
Filenames appear in the text like so:
dummy.c.Code, constants, and literals in the text appear like so:
main.Variable names appear in the text like so:
nBytes.Text on user interface labels or menus is shown as: Printer name, while buttons in user interfaces are shown as .
Menus and menu items are shown as: > .
Table of Contents
Chapters DFdiscover Software Installation, DFdiscover Acceptance Test Kit (ATK) Installation and Installation Completion are required for new and upgrade installations. Chapters HylaFAX Configuration, DFdiscover Configuration, and Integration Testing are required for new installations only. Implementation of Client Desktop Packages Installation will be dependent upon the packages that are included with the release. Chapter Study Installation is required only when a new study setup is available at the time of DFdiscover installation.
![[Important]](../../imagedata/important.png) | Execute chapters and steps in order |
|---|---|
|
All chapters and steps must be executed in document order. |
DFdiscover 2018 Version 5.1.0 is a minor release of DFdiscover 2018, having a major version number of 5, minor version number of 1 (the first minor version) and patch version number of 0 (this is not a patch). It contains everything needed for a complete installation.
The last chapter,
DFdiscover Installation Worksheet,
is an installation worksheet that should be completed at the same time as
the installation is being performed.
Use of the worksheet will confirm that no steps are missed and can
subsequently be used as a part of documentation for installation
qualification.
If a step is not relevant or not required, mark that location of
the worksheet NA (or stroke through it),
rather than leaving it blank.
Procedures in the body of the guide that must be recorded on the worksheet are marked with [CC##], a cross-reference symbol (XREF), where CC is an acronym for the chapter name and ## is a sequence number for the step within the chapter.
Table of Contents
This chapter ensures that the individuals responsible for DFdiscover have been identified, the materials necessary for the install are available, configures the UNIX environment of the server, and then steps through the installation of the major version.
A successful DFdiscover installation and subsequent properly maintained DFdiscover environment requires the commitment of personnel with different skills. It is essential that these personnel be identified in advance and be trained in the relevant aspects of DFdiscover. The following is a minimal set of job functions for which personnel must be identified. On the worksheet, record the names of one or more staff that will fill each job function. It is entirely acceptable for a single individual to perform more than one of the job functions.
UNIX administrator [SI50] . This job function includes maintenance of the hardware and operating system, supervision of and planning for resources such as disk storage and printers, administration of HylaFAX and modems, supervision of cron jobs, installation of application software and any updates, backup and recovery of data, and the creation of UNIX user accounts. The primary contact is the DFdiscover administrator. Typically this job requires 0.1 FTE.
DFdiscover administrator [SI51] . This job function includes registration of new studies to DFdiscover, administration of user privileges within DFdiscover, starting and stopping of study databases, and monitoring of study database consistency. Typically this job requires 0.1 FTE.
Study setup [SI52] . This job function is responsible for the definition of the study database to DFdiscover which minimally includes importing of the CRFs for setup, definition of variable styles and variables, specification of visit scheduling, and entry of participating centers information. This job function may also be involved in the initial creation of CRFs.
Programmer [SI53] . The programmer is responsible for creating any custom logic checks (referred to as edit checks within DFdiscover) and possibly executing them in batch, creating any study-specific reports, and defining lookup or coding tables.
SAS specialist [SI54] . This job function is responsible for creating DFsas specification files, executing them in DFdiscover, and subsequently processing the results in SAS®. This job function may also get involved in the definition of variable names, data types, and coding, and hence may liaise with the study setup job function.
Data entry [SI55] . This job function performs initial (and possibly second, or double data entry) review of received CRFs, verifying the data that was read by ICR, entering data that was not read, adding Queries where necessary, and identifying and resolving duplicates when they occur.
Higher-level data review [SI56] . This job function performs additional data reviews after entry. The focus is on data quality, completeness, and consistency.
Before beginning installation, the following steps must be completed as they gather information necessary for the install.
-
Record the full company name on the worksheet [SI00].
-
Record the DFdiscover software release on the worksheet [SI01].
Release numbers are of the form
X.Y.Z.![[Important]](../../imagedata/important.png)
Software Release These installation instructions are for a specific DFdiscover software release only. Confirm that the software release number on the download matches the software release number at the head of this document.
Record today's date on the worksheet [SI02].
Determine the name of the contact person [SI03], the server hostname [SI04], and the version of operating system on the server [SI05]. The contact person, in accordance with the DFdiscover License Agreement, should be the DFdiscover administrator or the DFdiscover software user consultant, and will be the primary liaison between end users and DF/Net Research, Inc..
Confirm the name of a printer that can be accessed from the DFdiscover environment [SI08].
Confirm that www.dfnetresearch.com can be accessed for obtaining the software release, patches and other downloads [SI09].
Confirm that the computer that will be running the DFdiscover software is able to send email externally, for example to DF/Net Research, Inc. (
<support@datafax.com>) [SI57].Record the telephone number of an existing, paper fax machine in the vicinity of the DFdiscover installation [SI12]. This will simplify fax send and receive testing.
If you will be using HylaFAX for fax handling, confirm that at least one of the telephone lines for incoming and outgoing DFdiscover faxes has been installed [SI10]. Record this DFdiscover telephone number [SI11] and also whether this is a direct, outward dialing line, or whether it passes through an internal PBX (what digit(s), if any, must be dialed to pass through the PBX? [SI58]).
The following materials are required for installation:
these installation notes [SI13]
the super-user password for the server machine [SI14]
the current DFdiscover software release [SI15]
a copy of the current DFdiscover Release Notes [SI16]
a copy of the Installation and Initialization chapter of the DFdiscover Acceptance Test Kit documentation [SI18]
a DFdiscover License Renewal form (or email) [SI21] with a valid license and expiration date for the server host identifier.
Transcribe the values from the form/email to the worksheet: hostid [SI37] , hostname [SI38] , # of users [SI39] , expiry date [SI40] , features [SI42] , password [SI41]
a support username [SI22] and support password [SI23] that will grant access to the support section of www.dfnetresearch.com
If the first study setup is being supplied by DF/Net Research, Inc., the study setup [SI24] is also required.
The steps in this section require the DFdiscover software media from download and super-user privileges.
This section is skipped for a new installation or when upgrading from release 3.8 or later.
![[Important]](../../imagedata/important.png) | Important |
|---|---|
The steps in this section are required for an upgrade installation from releases prior to 3.7-004 and must be completed before re-starting DFdiscover for the first time. |
The steps in this section require super-user privileges.
The permissions structures have been extended significantly beginning with the 3.8 release and existing user and permission definitions must be migrated to these new structures. To assist with this migration, DFuserdb, has been included with the release.
To migrate existing user permissions to the new structures [SI60], execute:
# /opt/dfdiscover/bin/DFuserdb -migrate
The program creates /opt/dfdiscover/lib/DFuserdb.log,
the new permissions structure, and archives the old files which are no longer
needed, for example /opt/dfdiscover/lib/DFperm.
After the program has run, an administrator should review the migrated
user and role definitions via DFadmin.
In particular, they may choose to assign more meaningful role names to those
generated by DFuserdb.
More information about DFuserdb can be found in
Programmer Guide, DFuserdb.
DFdiscover 2018 is supported on Novell openSUSE version 13.2 and newer, Leap 42.1 and newer, SUSE Tumbleweed and Redhat Enterprise Linux up to version 7.2 or newer. DFdiscover is a 64-bit server application - it installs on the 64-bit versions of any of these Linux distributions. It will not run on 32-bit systems. Other Linux distributions may work, but are unsupported. Debian distributions such as Ubuntu will not work at this time. CentOS and Oracle Linux are clones of RHEL and will work as expected.
If this is a new installation, DO NOT CREATE a
datafaxuser account or/opt/dfdiscoverdirectory. These tasks are completed automatically by the installer. The installer also adds the DFdiscover executables to the system-wide path and installs DFdiscover as a systemd service.-
If this is an upgrade of a DataFax server, there are several important changes that will be performed on your system. It is HIGHLY recommended that you have a complete backup or snapshot of your server prior to upgrading. Ensure that the
datafaxaccount is not in use as the installer moves/opt/datafaxto/opt/dfdiscoverand resets thedatafaxaccount home directory to the new file structure. The systemwide path to the software is automatically adjusted. Existing configuration files are automatically adjusted to match the new file structure.
Download and save the software rpm, from www.dfnetresearch.com to a local hard drive. Log into your server as
root.If this is an upgrade, stop DataFax, and erase the current version.
A complete installation will require approximately 1.7 Gb of free disk space for the software and documentation. The software will be installed into
/opt/dfdiscover. Record the installation directory [SI32].Execute the installation command appropriate for the operating system.
On openSUSE, use zypper, which will automatically download and install any dependencies required:
#zypper --no-gpg-checks install dfdiscover-5.1-0.x86_64.rpmOn RHEL, first install the epel-release repo (if you haven't already) as follows:
#yum install epel-releaseThen install DFdiscover using yum:
#yum --nogpgcheck install dfdiscover-5.1-0.x86_64.rpm
Record that the Linux installation completed successfully on the worksheet [LX00].
![[Note]](../../imagedata/note.png) | Note |
|---|---|
|
If you are upgrading from 3.8 or later and already have a valid certificate, you can skip this step. If you have acquired a certificate from a commercial CA, you can skip this step. |
The steps in this section require super-user privileges.
DFexplore and other DFdiscover client applications communicate with the DFdiscover server using TLS (Transport Layer Security, specifically TLS v1.2, in the same way that Internet banking sites do. TLS provides an encrypted path through the internet that prevents eavesdropping and modification of your data by third parties. Each DFdiscover client checks that it is communicating with the correct DFdiscover server by means of a certificate which encodes the DFdiscover server's name and ownership. This certificate is generated by choosing a very large random number (a key), adding organizational ownership information to it and then requesting that DF/Net Research, Inc. certify this key as authentic. When an DFexplore client connects to the DFdiscover server, it asks for this certificate and can then determine whether it is communicating with the correct server.
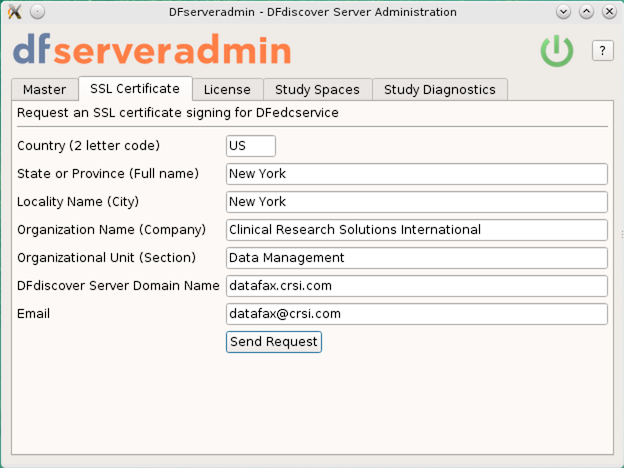
The process of generating a certificate starts with the execution of
DFserveradmin which generates the random number and then prompts
for required organizational information, including the country, state, organization
name and server name. Once this information has been provided, an email is
generated to <certreq@datafax.com>.
containing a request to certify that this is
an authentic DFdiscover server.
DF/Net Research, Inc. processes this request and emails back a small file
containing the certificate, which is then installed into the DFdiscover system.
Once this step has been completed, DFdiscover and DFexplore can be used.
Log in as super-user.
Use DFserveradmin to create the certificate request [CI01]
The certificate request is created with the DFserveradmin program. Click Request an SSL certificate signing for DFedcservice and enter the appropriate values for each of the fields.
Once you have entered the required data, click to submit the certificate signing request to DF/Net Research, Inc..![[Note]](../../imagedata/note.png)
Outgoing email The certificate signing request is emailed to DF/Net Research, Inc. from the machine where the DFserveradmin program was executed. This machine must be able to send email to the internet (in other words, outside of any corporate intranet). If that is not possible, the files
/tmp/cert.csr.txtand/tmp/cert.csrcan be transferred (use binary mode if doing this via ftp) to another machine and sent as attachments in an email to<certreq@datafax.com>.Wait for the certificate
This is the end of the procedure for generating a certificate request. You can expect an email with a signed certificate within 24 hours on business days.
In the interim, it is still possible to proceed as DFserveradmin also generates a self-signed certificate that is valid for 10 days.
Install Server Certificate
Determine install location
The server certificate must be installed in the location referenced by the
certificatekeyword in the/opt/dfdiscover/lib/DFedcservice.cffile. For example, thisDFedcservice.cffile:master localhost key /opt/discover/lib/edckey.pem certificate /opt/discover/lib/edccert.pem documentroot /opt/discover/edcdocs
identifies
/opt/discover/lib/edccert.pemas the location of the server certificate.Save the signed certificate [CI02]
The signed certificate will be emailed back to the email address that was specified as the
Email Addressin the certificate request procedure. Typically it will appear as a small (~1KB) attachment namededccert.pem.Save the attachment to the filename identified in the first step. If DFcertReq also generated a self-signed certificate, that certificate will be overwritten by this permanent, signed certificate.
This is the end of the steps necessary to request and install a server certificate.
The process of requesting and installing a DFdiscover license is described in this section.
DFdiscover is licensed on an annual basis for a specified maximum number of simultaneous users working on a uniquely identified DFdiscover server. Each license is unique to the combination of server identifier, features, expiry date, and number of licensed users. If any of these values changes, the existing license becomes invalid and a new license is required. Please note that if you are upgrading an existing DataFax server you will need to request a replacement license as the old license will no longer work once DFdiscover is installed. [1]
Request DFdiscover License
Determine server identifier
The unique server identifier [LI01] can be determined with the DFhostid command, as in:
#/opt/dfdiscover/bin/DFhostidThe output is a 20 character/digit identifier displayed in 5 blocks of 4. Note that the identifier will never contain any of 0 (zero), 1 (one), I (capital i), or O (capital o).
Forward server identifier to DF/Net Research, Inc.
Contact DF/Net Research, Inc. via telephone or email and provide them with this unique server identifier. Using the server identifier, and other license information including the expiry date, the number of licenses purchased, and any additional licensed features (such as web services or large study numbers), DF/Net Research, Inc. will generate a unique license. The license information will be emailed to the DFdiscover administrator.
-
The license will arrive in the body of an email message and have the following appearance:
hostid SG8D-QM2L-V8TK-PFB5-DDEG hostname <replace_with_your_hostname> nclients 12 expiration 20181231 password 2SQG-PGVG-BVXY-87BU-YYBL
features DFWS,LS
Save the license [LI03] to the file
/opt/dfdiscover/work/license(note the license will always be stored in this location, it is not customizable). Update hostname in DFdiscover License [LI04]
In the installed license, the value for the
hostnamekeyword must be updated. Edit the saved license and replace<replace_with_your_hostname>with the actual hostname of the server (this can be the fully qualified name or the nickname). Be careful to use the correct name and spell it correctly - if the hostname is inaccurate, DFdiscover will not start. Save the changes to the license file.
This step is applicable only if you have studies that were created in pre-2014 versions of DataFax. It must be performed by super-user.
DFdiscover
requires that studies from pre-2014.0.0 DataFax installations be migrated
using the DFmigrate program to take advantage of new features.
DFmigrate will determine
which steps need to be taken based on the version of DFdiscover that the
study is from. These changes may include moving edit checks to an
ecsrc directory and moving the lookup tables into a
lut directory.
-
To upgrade all studies on your system, as super-user run:
#/opt/dfdiscover/utils/DFmigrate -aThe following shows example output from this command:
********************************************************** DFmigrate: Study 254 - /opt/studies/val254 - Thu Apr 19 15:04:33 2018 ********************************************************** Step 1: Updating DFserver.cf ------------------------------------------------------------ File Converted: /opt/studies/val254/lib/DFserver.cf Step 2: Converting DFsetup ------------------------------------------------------------ File Converted: /opt/studies/val254/lib/DFsetup File Converted: /opt/studies/val254/lib/DFschema File Converted: /opt/studies/val254/lib/DFschema.stl File Converted: /opt/studies/val254/lib/DFtips Step 3: Moving Lookup Tables to lut directory ------------------------------------------------------------ Following lookup table files moved from study's lib to lut dir: aecodes.lut drugs.lut investigators.lut Step 4: Moving Edit Checks code to ecsrc directory ------------------------------------------------------------ DFedits already exist in ecsrc directory. Step 5: Converting postscript to png and old tiffs to png ------------------------------------------------------------ WARNING: PNG files already exist for plates: 1-11, 20. Study migration was successful. ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ DONE: Migration has been performed on the following study: 254 Please review dfmigrate_errors for any migration errors or warnings and/or manual steps that may be required. ~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~ #
In some cases (as in the example above), the background images used by DFprintdb will not be automatically converted. If you use DFprintdb and get a conversion error, you will need to re-import the backgrounds from the original PostScript® or PDF file using DFsetup.
Record that the pre-2014 studies migration completed successfully on the worksheet [MG00].
Congratulations! You have installed DFdiscover on your system. There are additional steps to be followed to ensure that your DFdiscover system is up-to-date and also to configure the various components. These are outlined in the following chapters.
[1] DFdiscover employs a floating license mechanism based on a unique host identifier, which requires one machine on the network to act as the central DFdiscover server. Choose a machine that is reliable (infrequently down) and is accessible by all potential DFdiscover client machines. If another server replaces the selected server in the future, a new license must be requested from DF/Net Research, Inc..
Table of Contents
This chapter covers the configuration of HylaFAX for sending and receiving faxes. If your installation will be using Protus (MyFax) you can skip this section.
![[Important]](../../imagedata/important.png) | Upgrade installation |
|---|---|
|
These steps are required for a new installation only. If this is an upgrade install, execute
then skip to DFdiscover Configuration. |
-
Determine which serial port(s) the fax modems will be connected to. You can configure HylaFAX to run on as many serial ports as are available and have fax modems for. A standard two-port machine uses the port names
/dev/term/aand/dev/term/b. Record the names on the worksheet [HC03]. Disable Port Services [HC04]
To prevent contention between the operating system's port services and HylaFAX, disable port services on the ports selected for use with HylaFAX. This can be easily accomplished using smc. For each selected port, disable the port service by ensuring that the toggle next to Service Enable is cleared.
HylaFAX is configured with the faxsetup program.
This program can be found in the
/opt/hylafax/bin directory.
faxsetup and faxaddmodem
Execute faxsetup [HC05]
Start faxsetup from a shell prompt:
#/opt/hylafax/sbin/faxsetupThe program leads you through the steps of initializing the HylaFAX environment. It is described completely in the HylaFAX document, Server Setup and Basic Configuration.
![[Note]](../../imagedata/note.png)
Note Messages from faxsetup indicating that /bin/vgetty or /bin/egetty do not exist can be safely ignored.
Except for the items in the following list, all of the defaults are correct and need only be acknowledged by pressing at each prompt. The defaults that may need to be changed are:
FaxMaster: the value must bedatafaxin installations where DFdiscover and HylaFAX co-exist on the same server (typical); otherwise,datafax@machinewheremachineis the hostname of the DFdiscover server.Country Code: in North America, enter1; elsewhere, enter the local country codeArea Code: the value must be the local area code
When faxsetup completes, it asks to configure modems. Respond
yto invoke faxaddmodem automatically.Execute faxaddmodem [HC06]
faxaddmodem is invoked automatically by the termination step of faxsetup, or it can be invoked manually with the command:
#/opt/hylafax/sbin/faxaddmodemSpecify device name
faxaddmodem requires the device name of the serial port to configure and asks for this information when the program starts. The device name in the response is the same as the real device name, without the leading
/dev/.Example 3.1. Device name for faxaddmodem
For the system device named
/dev/term/asupply the nameterm/aas the requested name. Similarly,/dev/tty0p0becomestty0p0.
-
The program is well described in the Server Setup and Basic Configuration document.
Again, most of the default options for the faxaddmodem program are correct.
Customize area code, fax number, and sender id
You will need to specify the area code, fax number, and sender identification string. Typically, the fax number and sender identification string are the same. Be careful not to use non-digit symbols in the sender id as some receiving machines will not like it. The recommended settings, for example, might be:
Area code [""]?
905Phone number of fax modem [+1.999.555.1212]?+1.905.555.1212Local id string (for TSI/SIG) ["DFdiscover"]?"1 905 555 1212"Ensure modem is correctly cabled and powered on
After confirming the server configuration parameters, faxaddmodem will attempt to communicate with the modem and then prompt for more configuration parameters. The modem must be cabled to the serial port and powered on at this point. The program determines an appropriate speed to converse with the modem and then interrogates it further. You can safely ignore the
hmmm, your modem seems to be hung
message.
Optional configuration for dial-prefix and adaptive answer
Finally, the modem configuration parameters are presented for confirmation. To specify a dial-prefix for outgoing calls, such as
9, and/or to disable adaptive answer, respondnoto the confirmation.To indicate that a dial-prefix is required for outgoing calls, the following setting must be changed:
Command for dialing [ATDT%s]?
ATDT9,%sand to disable adaptive answer, the next setting must also be changed [HC07]:
Command for setting up adaptive-answer [AT+FAA=1]?
AT+FAA=0For all of the other settings, the default is fine.
Repeat for next modem
As necessary, repeat faxaddmodem for each additional modem.
After all of the modems have been defined using faxaddmodem, inittab entries must be made to spawn processes that monitor the modems.
Create inittab entry for each serial port
Edit
/etc/inittabUse your favorite text editor to edit this file. The new entries will be added at the end of the file.
Add entry for each serial port
For each modem that was defined with faxaddmodem, a record must be added. The format of each record is:
fx0:234:respawn:/opt/hylafax/lib/fax/faxgetty tty0p0
The first column can contain any unique identifier string that is at most three characters in length and it must be different for each modem, e.g. fx0, fx1, fx2, etc. The argument to the last field of the record must be the same name of the device that was used when faxaddmodem was run.
Example 3.2. inittab entry for serial port
/dev/term/afx1:234:respawn:/opt/hylafax/lib/fax/faxgetty term/a
Save file
Save the changes made to
/etc/inittaband exit the editor [HC08].Restart the system init process
This process always has the process id of
1and it is most easily restarted with the command:#kill -1 1
The configuration of HylaFAX is complete.
The DFdiscover software installation includes a script that gracefully starts HylaFAX after the computer is booted, and conversely, gracefully halts HylaFAX before the computer is halted.
The script can be found in
/opt/dfdiscover/init.d/hylafax.
So that the script is available to the system when it boots or halts, it
must be installed in a known system location.
To install the HylaFAX startup script; [HC09]
#cp /opt/dfdiscover/init.d/hylafax /etc/init.d/hylafax#ln -s /etc/init.d/hylafax /etc/rc3.d/S99hylafax#ln -s /etc/init.d/hylafax /etc/rc1.d/K20hylafaxWith the script in place, start HylaFAX [HC10]
#/etc/init.d/hylafax stop#/etc/init.d/hylafax start
At this point, HylaFAX should be running and its status can be examined with the faxstat command. Type:
# /opt/hylafax/bin/faxstat -aThe output from the command will show the HylaFAX scheduler executing followed by one record for each defined modem [HC11].
Example 3.3. Output from faxstat for a system with a single modem
# /opt/hylafax/bin/faxstat -a
HylaFAX generates a significant amount of log information that can be useful debugging information should the need arise. The log information also records per fax details such as sender identification, duration of call, number of pages, and quality of transmission. This log information needs to be managed intelligently. HylaFAX provides two periodic maintenance scripts, faxqclean and faxcron that serve this purpose.
faxqclean should be configured to run once per day [HC12] while faxcron should run once per week [HC13]. The simplest way to achieve this is with the UNIX cron facility. The cron entries, for super-user, should look like:
0 1 * * * /opt/hylafax/sbin/faxqclean 0 2 * * 1 sh /opt/hylafax/sbin/faxcron | mail root
As super-user, add the cron entries.
For additional information, review General Tweaking and Customization Hints.
Table of Contents
![[Important]](../../imagedata/important.png) | Upgrade installation |
|---|---|
|
These steps are required for a new installation only. If this is an upgrade install, execute
to restart DFdiscover. Then complete Define DFdiscover capable printer and skip to Study Installation. |
This chapter completes the configuration of DFdiscover. After completing these steps, DFdiscover will be operational.
DFdiscover is able to print to printers that are either local to
the server or networked.
The printers must already be configured and named on the DFdiscover server,
which is typically a UNIX administration issue.
Given the set of printer names which are known to the system,
that complete set, or a subset thereof, needs to be configured in DFdiscover.
This is done by creating the file /opt/dfdiscover/lib/DFprinters.
Edit, or create,
/opt/dfdiscover/lib/DFprintersUse your favorite editor to edit this file.
Add default printer name first
Of all of the printers that have been identified as being DFdiscover capable, identify the one that will be the default, and add that printer name as the first line of the file. The order that the names appear in the file dictates the order in which they are displayed in any DFdiscover print dialog.
Add additional printers, if any
Each additional printer name should be added, one per line, following the default printer name.
Save file
Save the changes made to
/opt/dfdiscover//lib/DFprintersand exit the editor [DF10].
It's time to
start the DFdiscover services
[DF12].
Before doing so confirm that a valid DFdiscover license is installed in
/opt/dfdiscover/work/license.
To start the DFdiscover services, type:
% /opt/dfdiscover/bin/DFbootstrapThe output will be similar to the following:
DFmaster.rpcd: your software license expires in 365 days
1. Checking state of incoming daemons...
2. Checking /opt/dfdiscover/work/.dfincoming_work...
0 stale incoming entries obsoleted
3. Checking /opt/dfdiscover/incoming...
0 faxes awaiting processing.
DFmaster.rpcd: started.
Done.The DFdiscover services have now been started - continue with the next section. If an error prevents the DFdiscover services from starting, it is essential to fix the problem before continuing - the steps in the remaining sections will fail.
The remaining steps in this chapter must be executed by user datafax.
Exit the super-user shell and become user datafax.
Start the DFdiscover system administration application with the command:
% DFadminThe system administration application is used to configure the DFdiscover master process.
Configure DFdiscover Master [DF06]
Login to the DFdiscover administration application
If this is the first time that the administration application is used, enter the nickname or fully qualified name for the licensed DFdiscover server in the Server field. The Login Name is
datafaxand the Password ispasswd(this is a one-time password that must immediately be changed after authentication). Click .
Click to display the Master dialog
A complete description of the dialog and the meaning of the individual fields can be found in DFadmin System Administrator Guide, DFadmin - Master DFadmin - Master. Complete the fields as follows.
-
The default value for this field is the hostname of the DFdiscover server. If the default is not filled in, enter the hostname. Multiple hostnames (comma-delimited) are only required when multiple DFdiscover servers are available.
-
The value of this field is the name of a local printer. Typically, this should be the same default printer defined in [DF10].
Study-specific printers are defined at study creation time.
-
Select > to save the changes
The values specified in the dialog are saved.
Incoming and outgoing fax processsing is handled by third-party software: DFdiscover can work with either HylaFAX or the Protus fax service. DFdiscover communicates with the fax software or service by means of inbound and outbound processes that are configured using DFadmin.
At this point configure an incoming daemon [DF08] and configure an outgoing daemon [DF09]. A complete description of the configuration process can be found in DFadmin System Administrator Guide, DFadmin - TrafficDFadmin - Traffic.
The integration tests described in this chapter are recommended but not required. Their purpose is to demonstrate that incoming and outgoing faxing is operational, and that printing is correctly defined.
The purpose of this test is to demonstrate that an incoming fax can be received by DFdiscover, that it is properly archived, and that it can be viewed in DFexplore.
To demonstrate incoming fax operation
Fax a non-DFdiscover page from a plain paper machine
The purpose of this test is not to demonstrate that a CRF can be recognized as a study CRF, and so a simple cover page of any type is preferred. Fax the page from a traditional fax machine to the number that DFdiscover will receive faxes on [IN01].
Monitor the fax modem status lights (HylaFAX only)
During fax reception, various lights on the modem will flash or be illuminated. On Multitech modems the
OH(off-hook) light will be on during the fax reception and theRD(receive data) light will be flashing indicating that information is being received from the sending fax machine. When transmission is complete some of these lights will go out.-
Within 30 seconds (5 minutes for Protus fax service users) of the end of transmission, DFdiscover will create a new directory under the directory previously defined as the Archive Directory by Configure Incoming and Outgoing Processes. The directory name is 4-digits where the first two digits are the year within the century and the last two digits are the week within the year. The contents of the directory will be a single file with a 4-digit name, generally
0001. Confirm that the directory and file are present [IN02].Example 5.1. Confirmation of fax archival
In this case, the first fax was received on November 14, 2015 (the 46th week of 15). The archive directory was defined as
/opt/dfdiscover/archive.%cd /opt/dfdiscover/archive%ls%cd 1546%ls
-
Fax pages that are not barcoded as DFdiscover CRFs will be routed to a holding directory for subsequent manual identification.
Start DFexplore with the command:
%/opt/dfdiscover/bin/DFexploreAuthentication is required. Then click and confirm that the faxed page or pages are present [IN03].
-
Choose from the menu. In the Print dialog, select the Printer to which you want to print the page and choose to print the current page.
Confirm that the fax page prints successfully [IN04].
Completion of this section demonstrates that DFdiscover is able to receive faxes and process them.
The purpose of this test is to demonstrate that the previous editing done in Define DFdiscover capable printer was successful.
Identify a plain text file
Any text file will work for this test. The file should not be too large - the purpose of the test is to print a text file, not print hundreds of pages of text. A good default file is
/etc/passwd.Print the file
From a shell prompt, issue the command:
%/opt/dfdiscover/lib/DFprint_filter /etc/passwdpossibly substituting
/etc/passwdwith the name of the file that you chose to print.Confirm that the text file printed properly [IN05].
The purpose of this test is to demonstrate proper operation of the previously defined outgoing daemon.
This test will require the fax number of a local paper fax machine to be used as the fax destination.
Identify a plain text file
Any text file will work for this test. The file should not be too large - the purpose of the test is to fax a text file, not fax hundreds of pages of text. A good default file is
/etc/passwd.-
From a shell prompt, issue the command:
%DFsendfax /etc/passwdfaxnumberwhere
faxnumberis the fax number of the local paper fax machine.Depending upon the Polling Interval previously specified in the outgoing daemon configuration, it may take up to 60 seconds for DFdiscover to pass the queued fax to HylaFAX or the Protus fax service.
Confirm that the fax was sent successfully
Wait for a few minutes and confirm that the sent fax has arrived at the destination [IN06].
Table of Contents
This chapter is optional, and generally will not be executed at the time of DFdiscover installation.
The study installation steps described in this chapter will only apply to DFdiscover installations where a new study is ready to be installed at the same time.
To DFdiscover, a study definition comprises a parent directory and several sub-directories that hold study specific configuration information. As a result of this structure, a study definition can be easily transported by moving the parent directory to a new location. Everything that is needed by the study is contained within that parent directory.
![[Important]](../../imagedata/important.png) | Become super-user |
|---|---|
|
The steps in this section must be executed by super-user. |
Studies that are created by DF/Net Research, Inc. are typically distributed via download link, as a UNIX tar file. The procedure described here assumes this structure. Studies that are transported from other vendors or from affiliates within a company may be structured differently. This procedure may need to be modified to fit those specific conventions.
Study Installation
Pre-requisite: Create a parent directory for all studies
Generally, (but this is not a requirement) all DFdiscover studies exist under a common parent directory on the DFdiscover server. This directory is typically
/opt/studies. Create the parent directory, if necessary [SS01]:#mkdir -p /opt/studiesand update the ownership of the directory so that it is owned by
datafaxand groupstudies:#chown -R datafax /opt/studies#chgrp -R studies /opt/studies-
The remaining steps assume that the study tar image is available as
/tmp/study.tar[SS02]. Create a study folder and extract the contents of the tar image
A study setup from DF/Net Research, Inc. will be rooted at the study directory and is easily extracted with tar. Create the study folder and extract the tar image contents with commands similar to this [SS03]:
#cd /opt/studies#mkdirnewstudy#cdnewstudy#tar xpf /tmp/study.tarExample 6.1. Extracting study proto123
#cd /opt/studies#mkdir proto123#cd proto123#pwd#tar xpf /tmp/study.tar#
-
Update the file permissions and ownership of the extracted study
The owner and group permissions of the extracted study must be updated to reflect the ids for user
datafaxand groupstudiespresent on the installed system. Update the permissions with the chown and chgrp commands [SS04].Example 6.2. Updating ownership and permissions
#cd /opt/studies#chown -R datafax proto123#chgrp -R studies proto123
-
Register the study to DFdiscover
The local DFdiscover installation must now be made aware of the new study. This is accomplished by registering a new study with DFdiscover as described in DFadmin System Administrator Guide, StudyAddingAdding a New Study [SS05].
Performance of the procedure in this chapter is not required for the installation, but is highly recommended.
The DFdiscover Acceptance Test Kit is an important part of installation qualification. It allows the end-user to demonstrate that DFdiscover works in a manner that is in accordance with a known set of results.
The installation materials include a printed copy of the Installation and Initialization chapter of the DFdiscover Acceptance Test Kit documentation. These instructions represent the first of seventeen modules in the ATK, and are required for initialization [AT01]. A complete description of the remaining modules in the ATK is available after successful completion of the first module. In general, completion of all seventeen modules of the ATK requires one 8-hour day [AT02].
Table of Contents
DFdiscover includes a number of tools which are available for Windows 8/10 and OS X v10.11 or later. These can be obtained from www.dfnetresearch.com.
The current Windows 8/10 packages are:
DFdiscover_5_1_0.msi, containing DFexplore, DFsetup, DFadmin, DFbarcode, DFATK and several command-line tools.DFexplore_5_1_0.msi, containing only DFexplore.DFsend_5_1_0.msi, containing only DFsend.
The current OS X v10.11 or later packages are:
DFdiscover5.1.0.pkg, containing DFexplore, DFsetup, DFadmin, DFbarcode, DFATK and several command-line tools.DFexplore5.1.0.pkg, containing only DFexplore.DFsend5.1.0.pkg, containing only DFsend.
8.1. Windows client packages installation [PK01]
Installation and proper operation of the Windows client tools requires Windows 8/10.
The Windows client tools
are distributed as Windows msi installer files.
Locate the desired client package
msiThe file can be found on www.dfnetresearch.com in software releases support website.
Install from the desired client package
Double-click the desired client package file. Installation begins automatically and behaves similar to other Windows setup programs. The installer will add icons to the Desktop as well as entries in the menu.
![[Note]](../../imagedata/note.png) | Note |
|---|---|
Installation must be performed on the local drive of each Windows machine that is to run the client tools. |
8.2. DFdiscover barcoding plug-in for FrameMaker® installation [PK02]
Installation and proper operation of the DFdiscover Barcode plug-in requires:
FrameMaker 10 or greater,
Windows 8/10
![[Note]](../../imagedata/note.png) | Note |
|---|---|
Installation must be performed on the local drive of each machine that is running FrameMaker®, or on the shared drive if FrameMaker® was installed on a shared drive. |
The plug-in is distributed as barcodet.dll, a
Windows DLL.
The file can be found on www.dfnetresearch.com in
software releases support website.
The DLL must be copied to the
fminit directory below the
FrameMaker® product installation directory.
Use the same name for the copied file.
For example:
C:\copy "barcodet.dll" "C:\Program Files\Adobe\FrameMaker\fminit\barcodet.dll"
The FrameMaker® installation directory, typically
C:\Program Files\Adobe\FrameMaker
or C:\Users\username\AppData\Roaming\Adobe\FrameMaker\13\
(where 13 is the version number),
contains a product.ini file, typically maker.ini or
imaker.ini or fmsgml.ini,
depending upon the FrameMaker® version.
The [APIClients] section of this file lists the clients
to load when FrameMaker® starts.
Each client description is on a separate line and cannot contain line breaks.
A default FrameMaker® installation will already have an
[APIClients] section that ends with:
Mailer=Standard, Send Mail API Client, fminit\mailer.dll WordCount=DocReport,Count the number of words in the document, fminit\wordcnt.dll BookUtils=Standard, Book Utilities, fminit\bookutils.dll
Edit the maker.ini file with a text editor, locate the
[APIClients] section of the file, and add the following
text on a new line at the end of the section:
DFdiscover=Standard, DFdiscover Barcode Tool, fminit\barcodet.dll, all
Save and exit the maker.ini file.
Configuration is complete.
This procedure needs to be repeated on each computer that will use FrameMaker® to create CRFs for DFdiscover studies.
The installation and configuration of DFdiscover is now complete.
There are a few important items that are worth repeating
Collect together all installation materials and store them in a safe place [CL01]
If necessary, consult Installation Materials for the complete list.
Were all required items completed without error [CL02]?
If there are outstanding items that need input from DF/Net Research, Inc., see Getting Help.
Subscribe to the DFdiscover mailing list [CL03]
To review the instructions on how to complete this step, see DFdiscover Mailing List.
Sign the completed worksheet [CL04]
The worksheet is an important piece of documentation. Sign it and store it a safe location for future reference.
Finally, thank you for choosing DFdiscover and DF/Net Research, Inc.!
Table of Contents
- 10.1. DFdiscover Software Installation
- 10.1.1. Staffing
- 10.1.2. Before Installation
- 10.1.3. Installation Materials
- 10.1.4. Installation for Linux Systems
- 10.1.5. Migrate User Permissions (upgrade install, from versions older than 3.8, only)
- 10.1.6. Request and Install Server Certificate
- 10.1.7. Request and Install DFdiscover License
- 10.1.8. Migration of pre-2014 studies
- 10.2. HylaFAX Configuration
- 10.3. DFdiscover Configuration
- 10.4. Start DFdiscover
- 10.5. (Re-)configure DFdiscover Master
- 10.6. Configure Incoming and Outgoing Daemons
- 10.7. Integration Testing
- 10.8. Study Installation
- 10.9. DFdiscover Acceptance Test Kit (ATK) Installation
- 10.10. Client Desktop Package Installation
- 10.11. Installation Completion
- 10.12. Completion Sign-off
Use this worksheet as a permanent record of the installation's progress. When completed, sign and date this worksheet and store it together with any other installation qualification (IQ) materials.
Most of the entries in the worksheet require only a checkmark indicating that the step was completed. Some entries require the value of a parameter to be recorded. It is important to record these parameter values as they are assigned because in some cases they are referenced by subsequent steps.
| XREF | Parameter | Value |
|---|---|---|
| [SI00] | Company Name | |
| [SI01] | DFdiscover software release | 5.1.0 |
| [SI02] | Date | |
| [SI03] | Contact Person | |
| [SI04] | Server Hostname | |
| [SI05] | Server Operating System |
| XREF | Description | Completed? |
|---|---|---|
| [SI08] | the name of a printer that can be accessed from the DFdiscover environment | |
| [SI09] | www.dfnetresearch.com can be accessed | |
| [SI57] | send email externally,
for example to DF/Net Research, Inc. (<support@datafax.com>) | |
| [SI12] | telephone number of an existing, paper fax machine |
Cross the following section out if your installation will not be using HylaFAX to send and receive faxes.
| XREF | Parameter | Value |
|---|---|---|
| [SI10] | at least one of the telephone lines for incoming and outgoing DFdiscover faxes has been installed | |
| [SI11] | DFdiscover telephone number | |
| [SI58] | digit(s), if any, must be dialed to pass through the PBX? |
| XREF | Parameter | Value |
|---|---|---|
| [SI13] | installation notes | |
| [SI14] | super-user password | |
| [SI15] | current DFdiscover software release | |
| [SI16] | current DFdiscover Release Notes | |
| [SI18] | Installation and Initialization chapter of the DFdiscover Acceptance Test Kit documentation | |
| [SI21] | DFdiscover License Renewal form |
| XREF | Parameter | Value |
|---|---|---|
| [SI37] | hostid | |
| [SI38] | hostname | |
| [SI39] | # of users | |
| [SI40] | expiry date | |
| [SI42] | features | |
| [SI41] | password | |
| [SI22] | support username | |
| [SI23] | support password |
| XREF | Description | Completed? |
|---|---|---|
| [SI24] | study setup |
If you are not upgrading from a version older than 3.8, cross out this section.
| XREF | Description | Completed? |
|---|---|---|
| [SI60] | migrate existing user permissions to the new structures |
If you do not have any pre-2014 studies to migrate, cross out this section.
| XREF | Parameter | Value |
|---|---|---|
| [MG00] | pre-2014 studies migration completed successfully |
If you are not using HylaFAX for fax transmissions, cross out these sections.
| XREF | Parameter | Value |
|---|---|---|
| [HC03] | Identify Serial Ports |
| XREF | Description | Completed? |
|---|---|---|
| [HC04] | Disable Port Services |
| XREF | Description | Completed? |
|---|---|---|
| [HC11] | HylaFAX scheduler executing followed by one record for each defined modem |
| XREF | Description | Completed? |
|---|---|---|
| [DF10] | Define DFdiscover printers |
| XREF | Description | Completed? |
|---|---|---|
| [DF12] | start the DFdiscover services |
| XREF | Description | Completed? |
|---|---|---|
| [DF06] | Configure DFdiscover Master |
| XREF | Description | Completed? |
|---|---|---|
| [IN05] | Print a plain text file |
| XREF | Description | Completed? |
|---|---|---|
| [IN06] | Fax a plain text file |
Table of Contents
- A.1. External Software Copyrights
- A.1.1. DCMTK software package
- A.1.2. Jansson License
- A.1.3. HylaFAX Facsimile Software
- A.1.4. Mimencode
- A.1.5. RSA Data Security, Inc., MD5 message-digest algorithm
- A.1.6. mpack/munpack
- A.1.7. TIFF
- A.1.8. PostgreSQL
- A.1.9. OpenSSL License
- A.1.10. Original SSLeay License
- A.1.11. gawk
- A.1.12. Ghostscript
- A.1.13. MariaDB and FreeTDS
- A.1.14. QtAV
- A.1.15. FFmpeg
- A.1.16. c3.js
- A.1.17. d3.js
DFdiscover software uses several third-party software components as part of its server side and/or client tools.
The copyright information for each is provided below. If you would like to receive source codes of these third-party components, please send us your request at <support@datafax.com>.
Copyright Copyright © 1994-2011, OFFIS e.V. All rights reserved.
This software and supporting documentation were developed by
OFFIS e.V.
R&D Division Health
Eschereg 2
26121 Oldenburg, Germany
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
Neither the name of OFFIS nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
Copyright Copyright © 2009-2014 Petri Lehtinen <petri&digip.org>
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the “Software”), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Copyright Copyright © 1990-1996 Sam Leffler Copyright Copyright © 1991-1996 Silicon Graphics, Inc. HylaFAX is a trademark of Silicon Graphics, Inc.
Permission to use, copy, modify, distribute, and sell this software and its documentation for any purpose is hereby granted without fee, provided that (i) the above copyright notices and this permission notice appear in all copies of the software and related documentation, and (ii) the names of Sam Leffler and Silicon Graphics may not be used in any advertising or publicity relating to the software without the specific, prior written permission of Sam Leffler and Silicon Graphics.
THE SOFTWARE IS PROVIDED “AS-IS” AND WITHOUT WARRANTY OF ANY KIND, EXPRESS, IMPLIED OR OTHERWISE, INCLUDING WITHOUT LIMITATION, ANY WARRANTY OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. IN NO EVENT SHALL SAM LEFFLER OR SILICON GRAPHICS BE LIABLE FOR ANY SPECIAL, INCIDENTAL, INDIRECT OR CONSEQUENTIAL DAMAGES OF ANY KIND, OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER OR NOT ADVISED OF THE POSSIBILITY OF DAMAGE, AND ON ANY THEORY OF LIABILITY, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
Copyright Copyright © 1991 Bell Communications Research, Inc. (Bellcore)
Permission to use, copy, modify, and distribute this material for any purpose and without fee is hereby granted, provided that the above copyright notice and this permission notice appear in all copies, and that the name of Bellcore not be used in advertising or publicity pertaining to this material without the specific, prior written permission of an authorized representative of Bellcore. BELLCORE MAKES NO REPRESENTATIONS ABOUT THE ACCURACY OR SUITABILITY OF THIS MATERIAL FOR ANY PURPOSE. IT IS PROVIDED “AS IS”, WITHOUT ANY EXPRESS OR IMPLIED WARRANTIES.
Copyright Copyright © 1991-2, RSA Data Security, Inc. Created 1991. All rights reserved. License to copy and use this software is granted provided that it is identified as the “RSA Data Security, Inc. MD5 Message-Digest Algorithm” in all material mentioning or referencing this software or this function. License is also granted to make and use derivative works provided that such works are identified as “derived from the RSA Data Security, Inc. MD5 Message-Digest Algorithm” in all material mentioning or referencing the derived work. RSA Data Security, Inc. makes no representations concerning either the merchantability of this software or the suitability of this software for any particular purpose. It is provided “as is” without express or implied warranty of any kind. These notices must be retained in any copies of any part of this documentation and/or software.
Copyright © Copyright 1993,1994 by Carnegie Mellon University All Rights Reserved.
Permission to use, copy, modify, distribute, and sell this software and its documentation for any purpose is hereby granted without fee, provided that the above copyright notice appear in all copies and that both that copyright notice and this permission notice appear in supporting documentation, and that the name of Carnegie Mellon University not be used in advertising or publicity pertaining to distribution of the software without specific, written prior permission. Carnegie Mellon University makes no representations about the suitability of this software for any purpose. It is provided “as is” without express or implied warranty.
CARNEGIE MELLON UNIVERSITY DISCLAIMS ALL WARRANTIES WITH REGARD TO THIS SOFTWARE, INCLUDING ALL IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS, IN NO EVENT SHALL CARNEGIE MELLON UNIVERSITY BE LIABLE FOR ANY SPECIAL, INDIRECT OR CONSEQUENTIAL DAMAGES OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER IN AN ACTION OF CONTRACT, NEGLIGENCE OR OTHER TORTIOUS ACTION, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
Copyright Copyright © 1988-1997 Sam Leffler Copyright Copyright © 1991-1997 Silicon Graphics, Inc.
Permission to use, copy, modify, distribute, and sell this software and its documentation for any purpose is hereby granted without fee, provided that (i) the above copyright notices and this permission notice appear in all copies of the software and related documentation, and (ii) the names of Sam Leffler and Silicon Graphics may not be used in any advertising or publicity relating to the software without the specific, prior written permission of Sam Leffler and Silicon Graphics.
THE SOFTWARE IS PROVIDED “AS-IS” AND WITHOUT WARRANTY OF ANY KIND, EXPRESS, IMPLIED OR OTHERWISE, INCLUDING WITHOUT LIMITATION, ANY WARRANTY OF MERCHANTABILITY OR FITNESS FOR A PARTICULAR PURPOSE. IN NO EVENT SHALL SAM LEFFLER OR SILICON GRAPHICS BE LIABLE FOR ANY SPECIAL, INCIDENTAL, INDIRECT OR CONSEQUENTIAL DAMAGES OF ANY KIND, OR ANY DAMAGES WHATSOEVER RESULTING FROM LOSS OF USE, DATA OR PROFITS, WHETHER OR NOT ADVISED OF THE POSSIBILITY OF DAMAGE, AND ON ANY THEORY OF LIABILITY, ARISING OUT OF OR IN CONNECTION WITH THE USE OR PERFORMANCE OF THIS SOFTWARE.
Copyright © 1996-2014 by the PostgreSQL Global Development Group and is distributed under the terms of the license of the University of California below.
Postgres95 is Copyright © 1994-5 by the Regents of the University of California.
Permission to use, copy, modify, and distribute this software and its documentation for any purpose, without fee, and without a written agreement is hereby granted, provided that the above copyright notice and this paragraph and the following two paragraphs appear in all copies.
IN NO EVENT SHALL THE UNIVERSITY OF CALIFORNIA BE LIABLE TO ANY PARTY FOR DIRECT, INDIRECT, SPECIAL, INCIDENTAL, OR CONSEQUENTIAL DAMAGES, INCLUDING LOST PROFITS, ARISING OUT OF THE USE OF THIS SOFTWARE AND ITS DOCUMENTATION, EVEN IF THE UNIVERSITY OF CALIFORNIA HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. THE UNIVERSITY OF CALIFORNIA SPECIFICALLY DISCLAIMS ANY WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE SOFTWARE PROVIDED HEREUNDER IS ON AN “AS-IS” BASIS, AND THE UNIVERSITY OF CALIFORNIA HAS NO OBLIGATIONS TO PROVIDE MAINTENANCE, SUPPORT, UPDATES, ENHANCEMENTS, OR MODIFICATIONS.
Copyright Copyright © 1998-2016 The OpenSSL Project. All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
All advertising materials mentioning features or use of this software must display the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in .the OpenSSL Toolkit.” (http://www.openssl.org/)
The names “OpenSSL Toolkit” and "OpenSSL Project" must not be used to endorse or promote products derived from this software without prior written permission. For written permission, please contact openssl-core@openssl.org.
Products derived from this software may not be called “OpenSSL” nor may “OpenSSL” appear in their names without prior written permission of the OpenSSL Project.
Redistributions of any form whatsoever must retain the following acknowledgment: “This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit. (http://www.openssl.org)”
THIS SOFTWARE IS PROVIDED BY THE OpenSSL PROJECT “AS IS” AND ANY EXPRESSED OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE OpenSSL PROJECT OR ITS CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
This product includes cryptographic software written by Eric Young (<eay@cryptsoft.com>). This product includes software written by Tim Hudson (<tjh@cryptsoft.com>).
Copyright Copyright © 1995-1998 Eric Young (<eay@cryptsoft.com>)
All rights reserved.
This package is an SSL implementation written
by Eric Young (<eay@cryptsoft.com>).
The implementation was written so as to conform with Netscapes SSL.
This library is free for commercial and non-commercial use as long as
the following conditions are aheared to. The following conditions
apply to all code found in this distribution, be it the RC4, RSA,
lhash, DES, etc., code; not just the SSL code. The SSL documentation
included with this distribution is covered by the same copyright terms
except that the holder is Tim Hudson (<tjh@cryptsoft.com>).
Copyright remains Eric Young's, and as such any Copyright notices in the code are not to be removed. If this package is used in a product, Eric Young should be given attribution as the author of the parts of the library used. This can be in the form of a textual message at program startup or in documentation (online or textual) provided with the package.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met:
-
Redistributions of source code must retain the copyright notice, this list of conditions and the following disclaimer.
Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution.
All advertising materials mentioning features or use of this software must display the following acknowledgement: “This product includes cryptographic software written by Eric Young (
<eay@cryptsoft.com>)” The word “cryptographic” can be left out if the rouines from the library being used are not cryptographic related :-).If you include any Windows specific code (or a derivative thereof) from the apps directory (application code) you must include an acknowledgement: “This product includes software written by Tim Hudson (
<tjh@cryptsoft.com>)”
THIS SOFTWARE IS PROVIDED BY ERIC YOUNG “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE AUTHOR OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.
The licence and distribution terms for any publically available version or derivative of this code cannot be changed. i.e. this code cannot simply be copied and put under another distribution licence [including the GNU Public Licence.]
GNU GENERAL PUBLIC LICENSE Version 2, June 1991
http://www.gnu.org/licenses/gpl-2.0.html
Copyright Copyright © 1989, 1991 Free Software Foundation, Inc.
51 Franklin Street, Fifth Floor,
Boston, MA 02110-1301, USA
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
The licenses for most software are designed to take away your freedom to share and change it. By contrast, the GNU General Public License is intended to guarantee your freedom to share and change free software--to make sure the software is free for all its users. This General Public License applies to most of the Free Software Foundation's software and to any other program whose authors commit to using it. (Some other Free Software Foundation software is covered by the GNU Lesser General Public License instead.) You can apply it to your programs, too.
When we speak of free software, we are referring to freedom, not price. Our General Public Licenses are designed to make sure that you have the freedom to distribute copies of free software (and charge for this service if you wish), that you receive source code or can get it if you want it, that you can change the software or use pieces of it in new free programs; and that you know you can do these things.
To protect your rights, we need to make restrictions that forbid anyone to deny you these rights or to ask you to surrender the rights. These restrictions translate to certain responsibilities for you if you distribute copies of the software, or if you modify it.
For example, if you distribute copies of such a program, whether gratis or for a fee, you must give the recipients all the rights that you have. You must make sure that they, too, receive or can get the source code. And you must show them these terms so they know their rights.
We protect your rights with two steps: (1) copyright the software, and (2) offer you this license which gives you legal permission to copy, distribute and/or modify the software.
Also, for each author's protection and ours, we want to make certain that everyone understands that there is no warranty for this free software. If the software is modified by someone else and passed on, we want its recipients to know that what they have is not the original, so that any problems introduced by others will not reflect on the original authors' reputations.
Finally, any free program is threatened constantly by software patents. We wish to avoid the danger that redistributors of a free program will individually obtain patent licenses, in effect making the program proprietary. To prevent this, we have made it clear that any patent must be licensed for everyone's free use or not licensed at all.
The precise terms and conditions for copying, distribution and modification follow.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
This License applies to any program or other work which contains a notice placed by the copyright holder saying it may be distributed under the terms of this General Public License. The “Program”, below, refers to any such program or work, and a “work based on the Program” means either the Program or any derivative work under copyright law: that is to say, a work containing the Program or a portion of it, either verbatim or with modifications and/or translated into another language. (Hereinafter, translation is included without limitation in the term “modification”.) Each licensee is addressed as “you”.
Activities other than copying, distribution and modification are not covered by this License; they are outside its scope. The act of running the Program is not restricted, and the output from the Program is covered only if its contents constitute a work based on the Program (independent of having been made by running the Program). Whether that is true depends on what the Program does.
You may copy and distribute verbatim copies of the Program's source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on each copy an appropriate copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the absence of any warranty; and give any other recipients of the Program a copy of this License along with the Program.
You may charge a fee for the physical act of transferring a copy, and you may at your option offer warranty protection in exchange for a fee.
You may modify your copy or copies of the Program or any portion of it, thus forming a work based on the Program, and copy and distribute such modifications or work under the terms of Section 1 above, provided that you also meet all of these conditions:
You must cause the modified files to carry prominent notices stating that you changed the files and the date of any change.
-
You must cause any work that you distribute or publish, that in whole or in part contains or is derived from the Program or any part thereof, to be licensed as a whole at no charge to all third parties under the terms of this License.
If the modified program normally reads commands interactively when run, you must cause it, when started running for such interactive use in the most ordinary way, to print or display an announcement including an appropriate copyright notice and a notice that there is no warranty (or else, saying that you provide a warranty) and that users may redistribute the program under these conditions, and telling the user how to view a copy of this License. (Exception: if the Program itself is interactive but does not normally print such an announcement, your work based on the Program is not required to print an announcement.) These requirements apply to the modified work as a whole. If identifiable sections of that work are not derived from the Program, and can be reasonably considered independent and separate works in themselves, then this License, and its terms, do not apply to those sections when you distribute them as separate works. But when you distribute the same sections as part of a whole which is a work based on the Program, the distribution of the whole must be on the terms of this License, whose permissions for other licensees extend to the entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your rights to work written entirely by you; rather, the intent is to exercise the right to control the distribution of derivative or collective works based on the Program.
In addition, mere aggregation of another work not based on the Program with the Program (or with a work based on the Program) on a volume of a storage or distribution medium does not bring the other work under the scope of this License.
You may copy and distribute the Program (or a work based on it, under Section 2) in object code or executable form under the terms of Sections 1 and 2 above provided that you also do one of the following:
Accompany it with the complete corresponding machine-readable source code, which must be distributed under the terms of Sections 1 and 2 above on a medium customarily used for software interchange; or,
-
Accompany it with a written offer, valid for at least three years, to give any third party, for a charge no more than your cost of physically performing source distribution, a complete machine-readable copy of the corresponding source code, to be distributed under the terms of Sections 1 and 2 above on a medium customarily used for software interchange; or,
-
Accompany it with the information you received as to the offer to distribute corresponding source code. (This alternative is allowed only for noncommercial distribution and only if you received the program in object code or executable form with such an offer, in accord with Subsection b above.) The source code for a work means the preferred form of the work for making modifications to it. For an executable work, complete source code means all the source code for all modules it contains, plus any associated interface definition files, plus the scripts used to control compilation and installation of the executable. However, as a special exception, the source code distributed need not include anything that is normally distributed (in either source or binary form) with the major components (compiler, kernel, and so on) of the operating system on which the executable runs, unless that component itself accompanies the executable.
If distribution of executable or object code is made by offering access to copy from a designated place, then offering equivalent access to copy the source code from the same place counts as distribution of the source code, even though third parties are not compelled to copy the source along with the object code.
You may not copy, modify, sublicense, or distribute the Program except as expressly provided under this License. Any attempt otherwise to copy, modify, sublicense or distribute the Program is void, and will automatically terminate your rights under this License. However, parties who have received copies, or rights, from you under this License will not have their licenses terminated so long as such parties remain in full compliance.
You are not required to accept this License, since you have not signed it. However, nothing else grants you permission to modify or distribute the Program or its derivative works. These actions are prohibited by law if you do not accept this License. Therefore, by modifying or distributing the Program (or any work based on the Program), you indicate your acceptance of this License to do so, and all its terms and conditions for copying, distributing or modifying the Program or works based on it.
Each time you redistribute the Program (or any work based on the Program), the recipient automatically receives a license from the original licensor to copy, distribute or modify the Program subject to these terms and conditions. You may not impose any further restrictions on the recipients' exercise of the rights granted herein. You are not responsible for enforcing compliance by third parties to this License.
-
If, as a consequence of a court judgment or allegation of patent infringement or for any other reason (not limited to patent issues), conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot distribute so as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not distribute the Program at all. For example, if a patent license would not permit royalty-free redistribution of the Program by all those who receive copies directly or indirectly through you, then the only way you could satisfy both it and this License would be to refrain entirely from distribution of the Program.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the balance of the section is intended to apply and the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or to contest validity of any such claims; this section has the sole purpose of protecting the integrity of the free software distribution system, which is implemented by public license practices. Many people have made generous contributions to the wide range of software distributed through that system in reliance on consistent application of that system; it is up to the author/donor to decide if he or she is willing to distribute software through any other system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this License.
If the distribution and/or use of the Program is restricted in certain countries either by patents or by copyrighted interfaces, the original copyright holder who places the Program under this License may add an explicit geographical distribution limitation excluding those countries, so that distribution is permitted only in or among countries not thus excluded. In such case, this License incorporates the limitation as if written in the body of this License.
The Free Software Foundation may publish revised and/or new versions of the General Public License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Program specifies a version number of this License which applies to it and "any later version", you have the option of following the terms and conditions either of that version or of any later version published by the Free Software Foundation. If the Program does not specify a version number of this License, you may choose any version ever published by the Free Software Foundation.
If you wish to incorporate parts of the Program into other free programs whose distribution conditions are different, write to the author to ask for permission. For software which is copyrighted by the Free Software Foundation, write to the Free Software Foundation; we sometimes make exceptions for this. Our decision will be guided by the two goals of preserving the free status of all derivatives of our free software and of promoting the sharing and reuse of software generally. NO WARRANTY
BECAUSE THE PROGRAM IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE PROGRAM, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE PROGRAM “AS IS” WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. SHOULD THE PROGRAM PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
-
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE THE PROGRAM AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE PROGRAM (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE PROGRAM TO OPERATE WITH ANY OTHER PROGRAMS), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
The files in the base, psi, lib, toolbin, examples, doc and man directories (folders) and any subdirectories (sub-folders) thereof are part of GPL Ghostscript.
The files in the Resource directory and any subdirectories thereof are also part of GPL Ghostscript, with the explicit exception of the files in the CMap subdirectory (except “Identity-UTF16-H”, which is part of GPL Ghostscript). The CMap files are copyright Adobe Systems Incorporated and covered by a separate, GPL compatible license.
The files under the jpegxr directory and any subdirectories thereof are distributed under a no cost, open source license granted by the ITU/ISO/IEC but it is not GPL compatible - see jpegxr/COPYRIGHT.txt for details.
GPL Ghostscript is free software; you can redistribute it and/or modify it under the terms the GNU General Public License as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version.
GPL Ghostscript is distributed in the hope that it will be useful, but WITHOUT ANY WARRANTY; without even the implied warranty of MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the GNU General Public License for more details.
You should have received a copy of the GNU General Public License along with this program so you can know your rights and responsibilities. It should be in a file named doc/COPYING. If not, write to the
Free Software Foundation, Inc., 59 Temple Place Suite 330, Boston, MA
02111-1307, USA.
GPL Ghostscript contains an implementation of techniques covered by US Patents 5,055,942 and 5,917,614, and corresponding international patents. These patents are licensed for use with GPL Ghostscript under the following grant:
Whereas, Raph Levien (hereinafter “Inventor”) has obtained patent protection for related technology (hereinafter “Patented Technology”), Inventor wishes to aid the the GNU free software project in achieving its goals, and Inventor also wishes to increase public awareness of Patented Technology, Inventor hereby grants a fully paid up, nonexclusive, royalty free license to practice the patents listed below (“the Patents”) if and only if practiced in conjunction with software distributed under the terms of any version of the GNU General Public License as published by the
Free Software Foundation, 59 Temple Place, Suite
330, Boston, MA 02111.
Inventor reserves all other rights, including without limitation, licensing for software not distributed under the GNU General Public License.
5055942 Photographic image reproduction device using digital halftoning to para images allowing adjustable coarseness 5917614 Method and apparatus for error diffusion paraing of images with improved smoothness in highlight and shadow regions
GNU LESSER GENERAL PUBLIC LICENSE Version 2.1, February 1999 http://www.gnu.org/licenses/lgpl-2.1.html
Copyright Copyright © 1991, 1999
Free Software Foundation, Inc.
51 Franklin Street, Fifth Floor, Boston, MA 02110-1301 USA
Everyone is permitted to copy and distribute verbatim copies of this license document, but changing it is not allowed.
[This is the first released version of the Lesser GPL. It also counts as the successor of the GNU Library Public License, version 2, hence the version number 2.1.]
Preamble The licenses for most software are designed to take away your freedom to share and change it. By contrast, the GNU General Public Licenses are intended to guarantee your freedom to share and change free software--to make sure the software is free for all its users.
This license, the Lesser General Public License, applies to some specially designated software packages--typically libraries--of the Free Software Foundation and other authors who decide to use it. You can use it too, but we suggest you first think carefully about whether this license or the ordinary General Public License is the better strategy to use in any particular case, based on the explanations below.
When we speak of free software, we are referring to freedom of use, not price. Our General Public Licenses are designed to make sure that you have the freedom to distribute copies of free software (and charge for this service if you wish); that you receive source code or can get it if you want it; that you can change the software and use pieces of it in new free programs; and that you are informed that you can do these things.
To protect your rights, we need to make restrictions that forbid distributors to deny you these rights or to ask you to surrender these rights. These restrictions translate to certain responsibilities for you if you distribute copies of the library or if you modify it.
For example, if you distribute copies of the library, whether gratis or for a fee, you must give the recipients all the rights that we gave you. You must make sure that they, too, receive or can get the source code. If you link other code with the library, you must provide complete object files to the recipients, so that they can relink them with the library after making changes to the library and recompiling it. And you must show them these terms so they know their rights.
We protect your rights with a two-step method:
we copyright the library, and
-
we offer you this license, which gives you legal permission to copy, distribute and/or modify the library.
To protect each distributor, we want to make it very clear that there is no warranty for the free library. Also, if the library is modified by someone else and passed on, the recipients should know that what they have is not the original version, so that the original author's reputation will not be affected by problems that might be introduced by others.
Finally, software patents pose a constant threat to the existence of any free program. We wish to make sure that a company cannot effectively restrict the users of a free program by obtaining a restrictive license from a patent holder. Therefore, we insist that any patent license obtained for a version of the library must be consistent with the full freedom of use specified in this license.
Most GNU software, including some libraries, is covered by the ordinary GNU General Public License. This license, the GNU Lesser General Public License, applies to certain designated libraries, and is quite different from the ordinary General Public License. We use this license for certain libraries in order to permit linking those libraries into non-free programs.
When a program is linked with a library, whether statically or using a shared library, the combination of the two is legally speaking a combined work, a derivative of the original library. The ordinary General Public License therefore permits such linking only if the entire combination fits its criteria of freedom. The Lesser General Public License permits more lax criteria for linking other code with the library.
We call this license the "Lesser" General Public License because it does Less to protect the user's freedom than the ordinary General Public License. It also provides other free software developers Less of an advantage over competing non-free programs. These disadvantages are the reason we use the ordinary General Public License for many libraries. However, the Lesser license provides advantages in certain special circumstances.
For example, on rare occasions, there may be a special need to encourage the widest possible use of a certain library, so that it becomes a de-facto standard. To achieve this, non-free programs must be allowed to use the library. A more frequent case is that a free library does the same job as widely used non-free libraries. In this case, there is little to gain by limiting the free library to free software only, so we use the Lesser General Public License.
In other cases, permission to use a particular library in non-free programs enables a greater number of people to use a large body of free software. For example, permission to use the GNU C Library in non-free programs enables many more people to use the whole GNU operating system, as well as its variant, the GNU/Linux operating system.
Although the Lesser General Public License is Less protective of the users' freedom, it does ensure that the user of a program that is linked with the Library has the freedom and the wherewithal to run that program using a modified version of the Library.
The precise terms and conditions for copying, distribution and modification follow. Pay close attention to the difference between a “work based on the library” and a “work that uses the library”. The former contains code derived from the library, whereas the latter must be combined with the library in order to run.
TERMS AND CONDITIONS FOR COPYING, DISTRIBUTION AND MODIFICATION
-
This License Agreement applies to any software library or other program which contains a notice placed by the copyright holder or other authorized party saying it may be distributed under the terms of this Lesser General Public License (also called “this License”). Each licensee is addressed as “you”.
A “library” means a collection of software functions and/or data prepared so as to be conveniently linked with application programs (which use some of those functions and data) to form executables.
The “Library”, below, refers to any such software library or work which has been distributed under these terms. A “work based on the Library” means either the Library or any derivative work under copyright law: that is to say, a work containing the Library or a portion of it, either verbatim or with modifications and/or translated straightforwardly into another language. (Hereinafter, translation is included without limitation in the term “modification”.)
“Source code” for a work means the preferred form of the work for making modifications to it. For a library, complete source code means all the source code for all modules it contains, plus any associated interface definition files, plus the scripts used to control compilation and installation of the library.
Activities other than copying, distribution and modification are not covered by this License; they are outside its scope. The act of running a program using the Library is not restricted, and output from such a program is covered only if its contents constitute a work based on the Library (independent of the use of the Library in a tool for writing it). Whether that is true depends on what the Library does and what the program that uses the Library does.
You may copy and distribute verbatim copies of the Library's complete source code as you receive it, in any medium, provided that you conspicuously and appropriately publish on each copy an appropriate copyright notice and disclaimer of warranty; keep intact all the notices that refer to this License and to the absence of any warranty; and distribute a copy of this License along with the Library.
You may charge a fee for the physical act of transferring a copy, and you may at your option offer warranty protection in exchange for a fee.
You may modify your copy or copies of the Library or any portion of it, thus forming a work based on the Library, and copy and distribute such modifications or work under the terms of Section 1 above, provided that you also meet all of these conditions:
The modified work must itself be a software library.
You must cause the files modified to carry prominent notices stating that you changed the files and the date of any change.
You must cause the whole of the work to be licensed at no charge to all third parties under the terms of this License.
If a facility in the modified Library refers to a function or a table of data to be supplied by an application program that uses the facility, other than as an argument passed when the facility is invoked, then you must make a good faith effort to ensure that, in the event an application does not supply such function or table, the facility still operates, and performs whatever part of its purpose remains meaningful. (For example, a function in a library to compute square roots has a purpose that is entirely well-defined independent of the application. Therefore, Subsection 2d requires that any application-supplied function or table used by this function must be optional: if the application does not supply it, the square root function must still compute square roots.)
These requirements apply to the modified work as a whole. If identifiable sections of that work are not derived from the Library, and can be reasonably considered independent and separate works in themselves, then this License, and its terms, do not apply to those sections when you distribute them as separate works. But when you distribute the same sections as part of a whole which is a work based on the Library, the distribution of the whole must be on the terms of this License, whose permissions for other licensees extend to the entire whole, and thus to each and every part regardless of who wrote it.
Thus, it is not the intent of this section to claim rights or contest your rights to work written entirely by you; rather, the intent is to exercise the right to control the distribution of derivative or collective works based on the Library.
In addition, mere aggregation of another work not based on the Library with the Library (or with a work based on the Library) on a volume of a storage or distribution medium does not bring the other work under the scope of this License.
You may opt to apply the terms of the ordinary GNU General Public License instead of this License to a given copy of the Library. To do this, you must alter all the notices that refer to this License, so that they refer to the ordinary GNU General Public License, version 2, instead of to this License. (If a newer version than version 2 of the ordinary GNU General Public License has appeared, then you can specify that version instead if you wish.) Do not make any other change in these notices.
Once this change is made in a given copy, it is irreversible for that copy, so the ordinary GNU General Public License applies to all subsequent copies and derivative works made from that copy.
This option is useful when you wish to copy part of the code of the Library into a program that is not a library.
You may copy and distribute the Library (or a portion or derivative of it, under Section 2) in object code or executable form under the terms of Sections 1 and 2 above provided that you accompany it with the complete corresponding machine-readable source code, which must be distributed under the terms of Sections 1 and 2 above on a medium customarily used for software interchange.
If distribution of object code is made by offering access to copy from a designated place, then offering equivalent access to copy the source code from the same place satisfies the requirement to distribute the source code, even though third parties are not compelled to copy the source along with the object code.
A program that contains no derivative of any portion of the Library, but is designed to work with the Library by being compiled or linked with it, is called a "work that uses the Library". Such a work, in isolation, is not a derivative work of the Library, and therefore falls outside the scope of this License.
However, linking a "work that uses the Library" with the Library creates an executable that is a derivative of the Library (because it contains portions of the Library), rather than a “work that uses the library”. The executable is therefore covered by this License. Section 6 states terms for distribution of such executables.
When a “work that uses the Library” uses material from a header file that is part of the Library, the object code for the work may be a derivative work of the Library even though the source code is not. Whether this is true is especially significant if the work can be linked without the Library, or if the work is itself a library. The threshold for this to be true is not precisely defined by law.
If such an object file uses only numerical parameters, data structure layouts and accessors, and small macros and small inline functions (ten lines or less in length), then the use of the object file is unrestricted, regardless of whether it is legally a derivative work. (Executables containing this object code plus portions of the Library will still fall under Section 6.)
Otherwise, if the work is a derivative of the Library, you may distribute the object code for the work under the terms of Section 6. Any executables containing that work also fall under Section 6, whether or not they are linked directly with the Library itself.
As an exception to the Sections above, you may also combine or link a "work that uses the Library" with the Library to produce a work containing portions of the Library, and distribute that work under terms of your choice, provided that the terms permit modification of the work for the customer's own use and reverse engineering for debugging such modifications.
You must give prominent notice with each copy of the work that the Library is used in it and that the Library and its use are covered by this License. You must supply a copy of this License. If the work during execution displays copyright notices, you must include the copyright notice for the Library among them, as well as a reference directing the user to the copy of this License.
Also, you must do one of these things:
Accompany the work with the complete corresponding machine-readable source code for the Library including whatever changes were used in the work (which must be distributed under Sections 1 and 2 above); and, if the work is an executable linked with the Library, with the complete machine-readable "work that uses the Library", as object code and/or source code, so that the user can modify the Library and then relink to produce a modified executable containing the modified Library. (It is understood that the user who changes the contents of definitions files in the Library will not necessarily be able to recompile the application to use the modified definitions.)
Use a suitable shared library mechanism for linking with the Library. A suitable mechanism is one that
uses at run time a copy of the library already present on the user's computer system, rather than copying library functions into the executable, and
will operate properly with a modified version of the library, if the user installs one, as long as the modified version is interface-compatible with the version that the work was made with.
Accompany the work with a written offer, valid for at least three years, to give the same user the materials specified in Subsection 6a, above, for a charge no more than the cost of performing this distribution.
If distribution of the work is made by offering access to copy from a designated place, offer equivalent access to copy the above specified materials from the same place.
-
Verify that the user has already received a copy of these materials or that you have already sent this user a copy. For an executable, the required form of the “work that uses the Library” must include any data and utility programs needed for reproducing the executable from it. However, as a special exception, the materials to be distributed need not include anything that is normally distributed (in either source or binary form) with the major components (compiler, kernel, and so on) of the operating system on which the executable runs, unless that component itself accompanies the executable.
It may happen that this requirement contradicts the license restrictions of other proprietary libraries that do not normally accompany the operating system. Such a contradiction means you cannot use both them and the Library together in an executable that you distribute.
You may place library facilities that are a work based on the Library side-by-side in a single library together with other library facilities not covered by this License, and distribute such a combined library, provided that the separate distribution of the work based on the Library and of the other library facilities is otherwise permitted, and provided that you do these two things:
Accompany the combined library with a copy of the same work based on the Library, uncombined with any other library facilities. This must be distributed under the terms of the Sections above.
Give prominent notice with the combined library of the fact that part of it is a work based on the Library, and explaining where to find the accompanying uncombined form of the same work.
You may not copy, modify, sublicense, link with, or distribute the Library except as expressly provided under this License. Any attempt otherwise to copy, modify, sublicense, link with, or distribute the Library is void, and will automatically terminate your rights under this License. However, parties who have received copies, or rights, from you under this License will not have their licenses terminated so long as such parties remain in full compliance.
You are not required to accept this License, since you have not signed it. However, nothing else grants you permission to modify or distribute the Library or its derivative works. These actions are prohibited by law if you do not accept this License. Therefore, by modifying or distributing the Library (or any work based on the Library), you indicate your acceptance of this License to do so, and all its terms and conditions for copying, distributing or modifying the Library or works based on it.
Each time you redistribute the Library (or any work based on the Library), the recipient automatically receives a license from the original licensor to copy, distribute, link with or modify the Library subject to these terms and conditions. You may not impose any further restrictions on the recipients' exercise of the rights granted herein. You are not responsible for enforcing compliance by third parties with this License.
If, as a consequence of a court judgment or allegation of patent infringement or for any other reason (not limited to patent issues), conditions are imposed on you (whether by court order, agreement or otherwise) that contradict the conditions of this License, they do not excuse you from the conditions of this License. If you cannot distribute so as to satisfy simultaneously your obligations under this License and any other pertinent obligations, then as a consequence you may not distribute the Library at all. For example, if a patent license would not permit royalty-free redistribution of the Library by all those who receive copies directly or indirectly through you, then the only way you could satisfy both it and this License would be to refrain entirely from distribution of the Library.
If any portion of this section is held invalid or unenforceable under any particular circumstance, the balance of the section is intended to apply, and the section as a whole is intended to apply in other circumstances.
It is not the purpose of this section to induce you to infringe any patents or other property right claims or to contest validity of any such claims; this section has the sole purpose of protecting the integrity of the free software distribution system which is implemented by public license practices. Many people have made generous contributions to the wide range of software distributed through that system in reliance on consistent application of that system; it is up to the author/donor to decide if he or she is willing to distribute software through any other system and a licensee cannot impose that choice.
This section is intended to make thoroughly clear what is believed to be a consequence of the rest of this License.
-
If the distribution and/or use of the Library is restricted in certain countries either by patents or by copyrighted interfaces, the original copyright holder who places the Library under this License may add an explicit geographical distribution limitation excluding those countries, so that distribution is permitted only in or among countries not thus excluded. In such case, this License incorporates the limitation as if written in the body of this License.
-
The Free Software Foundation may publish revised and/or new versions of the Lesser General Public License from time to time. Such new versions will be similar in spirit to the present version, but may differ in detail to address new problems or concerns.
Each version is given a distinguishing version number. If the Library specifies a version number of this License which applies to it and "any later version", you have the option of following the terms and conditions either of that version or of any later version published by the Free Software Foundation. If the Library does not specify a license version number, you may choose any version ever published by the Free Software Foundation.
If you wish to incorporate parts of the Library into other free programs whose distribution conditions are incompatible with these, write to the author to ask for permission. For software which is copyrighted by the Free Software Foundation, write to the Free Software Foundation; we sometimes make exceptions for this. Our decision will be guided by the two goals of preserving the free status of all derivatives of our free software and of promoting the sharing and reuse of software generally.
NO WARRANTY
BECAUSE THE LIBRARY IS LICENSED FREE OF CHARGE, THERE IS NO WARRANTY FOR THE LIBRARY, TO THE EXTENT PERMITTED BY APPLICABLE LAW. EXCEPT WHEN OTHERWISE STATED IN WRITING THE COPYRIGHT HOLDERS AND/OR OTHER PARTIES PROVIDE THE LIBRARY "AS IS" WITHOUT WARRANTY OF ANY KIND, EITHER EXPRESSED OR IMPLIED, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE LIBRARY IS WITH YOU. SHOULD THE LIBRARY PROVE DEFECTIVE, YOU ASSUME THE COST OF ALL NECESSARY SERVICING, REPAIR OR CORRECTION.
IN NO EVENT UNLESS REQUIRED BY APPLICABLE LAW OR AGREED TO IN WRITING WILL ANY COPYRIGHT HOLDER, OR ANY OTHER PARTY WHO MAY MODIFY AND/OR REDISTRIBUTE THE LIBRARY AS PERMITTED ABOVE, BE LIABLE TO YOU FOR DAMAGES, INCLUDING ANY GENERAL, SPECIAL, INCIDENTAL OR CONSEQUENTIAL DAMAGES ARISING OUT OF THE USE OR INABILITY TO USE THE LIBRARY (INCLUDING BUT NOT LIMITED TO LOSS OF DATA OR DATA BEING RENDERED INACCURATE OR LOSSES SUSTAINED BY YOU OR THIRD PARTIES OR A FAILURE OF THE LIBRARY TO OPERATE WITH ANY OTHER SOFTWARE), EVEN IF SUCH HOLDER OR OTHER PARTY HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
Copyright © Wang Bin <wbsecg1@gmail.com>
Shanghai University->S3 Graphics->Deepin, Shanghai, China
2013-01-21
**QtAV is free software licensed under the term of LGPL v2.1. The player example is licensed under GPL v3. If you use QtAV or its constituent libraries, you must adhere to the terms of the license in question.**
Rather than repeating the text of the LGPL v2.1, the original text can be found in GNU LESSER GENERAL PUBLIC LICENSE, Version 2.1.
Most files in FFmpeg are under the GNU Lesser General Public License version 2.1 or later (LGPL v2.1+). Read the file `COPYING.LGPLv2.1` for details. Some other files have MIT/X11/BSD-style licenses. In combination the LGPL v2.1+ applies to FFmpeg.
Rather than repeating the text of the LGPL v2.1, the original text can be found in GNU LESSER GENERAL PUBLIC LICENSE, Version 2.1.
The MIT License (MIT) Copyright © 2013 Masayuki Tanaka
Permission is hereby granted, free of charge, to any person obtaining a copy of this software and associated documentation files (the "Software"), to deal in the Software without restriction, including without limitation the rights to use, copy, modify, merge, publish, distribute, sublicense, and/or sell copies of the Software, and to permit persons to whom the Software is furnished to do so, subject to the following conditions:
The above copyright notice and this permission notice shall be included in all copies or substantial portions of the Software.
THE SOFTWARE IS PROVIDED “AS IS”, WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED, INCLUDING BUT NOT LIMITED TO THE WARRANTIES OF MERCHANTABILITY, FITNESS FOR A PARTICULAR PURPOSE AND NONINFRINGEMENT. IN NO EVENT SHALL THE AUTHORS OR COPYRIGHT HOLDERS BE LIABLE FOR ANY CLAIM, DAMAGES OR OTHER LIABILITY, WHETHER IN AN ACTION OF CONTRACT, TORT OR OTHERWISE, ARISING FROM, OUT OF OR IN CONNECTION WITH THE SOFTWARE OR THE USE OR OTHER DEALINGS IN THE SOFTWARE.
Copyright 2010-2017 Mike Bostock All rights reserved.
Redistribution and use in source and binary forms, with or without modification, are permitted provided that the following conditions are met: * Redistributions of source code must retain the above copyright notice, this list of conditions and the following disclaimer. * Redistributions in binary form must reproduce the above copyright notice, this list of conditions and the following disclaimer in the documentation and/or other materials provided with the distribution. * Neither the name of the author nor the names of contributors may be used to endorse or promote products derived from this software without specific prior written permission.
THIS SOFTWARE IS PROVIDED BY THE COPYRIGHT HOLDERS AND CONTRIBUTORS “AS IS” AND ANY EXPRESS OR IMPLIED WARRANTIES, INCLUDING, BUT NOT LIMITED TO, THE IMPLIED WARRANTIES OF MERCHANTABILITY AND FITNESS FOR A PARTICULAR PURPOSE ARE DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT OWNER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE.